Network · Secure Messaging
Encrypted messaging that gates itself.
Six-state BAA lifecycle controls messaging access automatically. No manual intervention. No accidental ePHI to a vendor without a BAA. The gate is the architecture.
HIPAA mapping
What this satisfies in the Security Rule.
4 citations, each with the specific Secure Messaging behavior that satisfies it. The mapping is the receipt — what you can show an auditor without assembling anything new.
§164.312(e)Transmission security
Implements technical security measures to guard against unauthorized access to ePHI being transmitted over an electronic network. The platform's TLS 1.3 plus AES-256-GCM encryption satisfies this directly.
§164.312(e)(2)(ii)Encryption
Implements a mechanism to encrypt ePHI whenever deemed appropriate. Always-on encryption removes the “deemed appropriate” judgment.
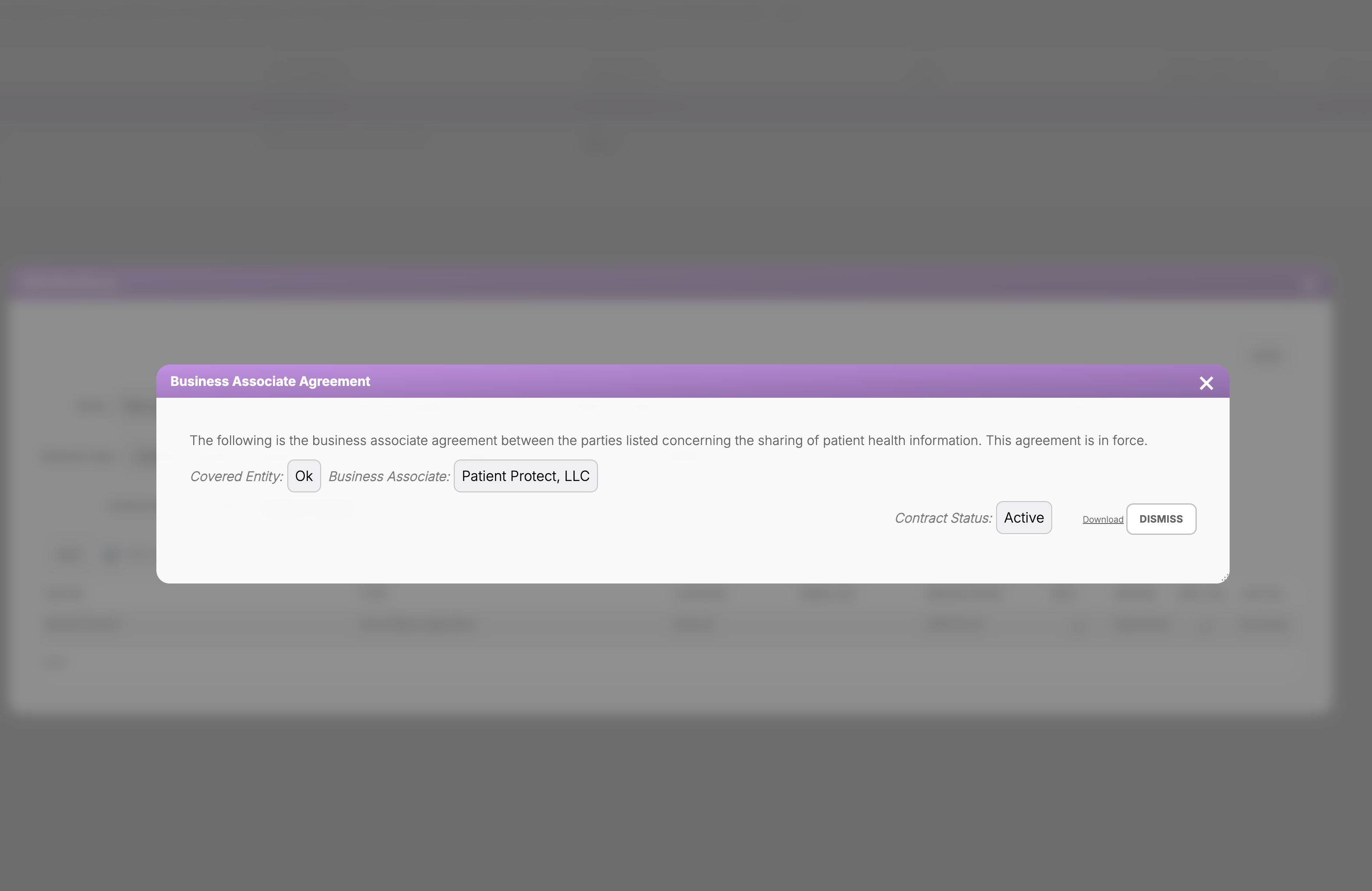
§164.502(e)Disclosures to business associates
Permits disclosure to a BA only when satisfactory assurances are in place (the BAA). The gate enforces this — no BAA, no ePHI through messaging.
§164.504(e)Business associate contracts
Specifies required BAA contents. The platform's BAA workflow aligns with §164.504(e) requirements.
What it does
Encryption is solved. Governance is the actual problem.
The HIPAA messaging problem isn't encryption. Encryption is solved. The problem is governance — knowing whether the recipient is covered by a BAA, knowing whether the BAA is current, knowing whether the content type is appropriate for the recipient. Most “HIPAA-compliant messaging” tools encrypt the messages and leave the governance to the practice.
Patient Protect's messaging gates itself. The platform reads BAA state from the Workforce module continuously. Messages to vendors with Active BAAs flow normally. Messages to vendors without Active BAAs are gated — content masked, attachments blocked, ePHI exchange prevented at the architecture layer. The governance is in the platform, not the practice's memory.
The gate is symmetric. The vendor's side of the conversation is also gated when the BAA isn't Active. Both parties are prevented from sending ePHI when the contract isn't in force.
How it works
6 mechanisms keep Secure Messaging working.
BAA-aware compose.
Compose to a vendor reads the vendor's BAA state. If the BAA is anything other than Active, the compose interface shows a warning before the workforce member invests time writing. If they proceed, the send action is blocked with an explanation and a link to the BAA record.
Six-state BAA lifecycle integration.
The messaging gate reads from the same six-state lifecycle the Vendor Risk Scanner uses (None, Staging, Pending, Active, Expired, Revoked). State transitions are reflected in messaging gate state immediately — no batch refresh.
Always-on encryption.
TLS 1.3 in transit. AES-256-GCM at rest. No “encryption optional” mode. Encryption is uniform across messaging types (workforce-to-workforce, workforce-to-vendor, workforce-to-patient).
Patient messaging with consent gates.
Patient messaging requires acknowledged consent in the patient's record. Patients without consent acknowledgment can still receive non-PHI administrative messages (appointment reminders without medical context); PHI-bearing messages require active consent.
Attachment validation.
Attachments are validated for type and scanned for malicious content before delivery. Attachment delivery is BAA-gated the same way text content is — vendors without Active BAAs cannot receive attachments containing ePHI.
Audit on every message.
Every message generates audit log entries — sender, recipient, timestamp, content category (whether PHI was involved). The audit makes “did we ever send X to vendor Y?” a one-query answer.
Who this is for
Built for the practices that need it most.
Practices that exchange ePHI with vendors regularly.
Billing services, transcription, lab interfaces, IT vendors — vendors that handle ePHI as part of their normal function. The gate is most valuable for these high-frequency relationships where the cost of a missed BAA is highest.
Practices recovering from a BAA-related incident.
If your office has had a finding involving ePHI sent to a vendor without an active BAA, the architectural gate is the remediation. The platform makes the failure mode impossible forward.
Practices replacing email-with-encryption.
Practices that have been using “secure email” or third-party encryption tools for vendor communication often hit governance gaps. The platform's integrated gate is the replacement — messaging plus governance plus audit in one workflow.
Practices that exchange ePHI with patients.
Patient messaging is the operational alternative to phone tag and to portal logins. Encrypted, BAA-acknowledgment-gated, audit-logged.
Connected to
No module is an island.
Secure Messagingworks because it's connected. Every signal feeds another module; every closure becomes evidence somewhere else.
Defense layer
Vendor Risk Scanner
The BAA lifecycle that drives the messaging gate is managed in the Vendor Risk Scanner.
Learn moreNetwork layer
Smart Referrals
Referral communication uses Secure Messaging with referral-context gates.
Learn moreNetwork layer
Patient Management
Patient messaging integrates with patient records; messages feed the patient's record audit.
Learn moreWhat you get
6outcomes you'll feel in week one.
No accidental ePHI without a BAA.
The gate is architectural; the failure mode is impossible.
Always-on encryption.
TLS 1.3 in transit, AES-256-GCM at rest. No opt-in, no opt-out.
Six-state lifecycle.
None / Staging / Pending / Active / Expired / Revoked — explicit at every moment.
Symmetric gating.
Both office and vendor are blocked when the BAA isn't Active.
Patient messaging with consent gates.
Patient PHI exchange requires active acknowledgment.
Audit on every message.
Sender, recipient, timestamp, content category — defensible record.
What happens to past messages when a BAA expires?
Can patients message us first?
What if a vendor refuses to use Patient Protect?
Are messages stored forever?
Can workforce members see each other's messages?
What about file sizes?
Continue exploring
Related features in the platform.
Defense
Vendor Risk Scanner
Evaluates every business associate against your current standing. The vendor risk picture stays current as your BAAs and their behavior do.
Learn moreNetwork
Smart Referrals
Refer with full audit trail. Every send, every acceptance, every consultation. Compliance documentation that builds itself.
Learn moreNetwork
Patient Management
One place for patient records. Role-based access. Every view, edit, export logged automatically. The audit trail builds itself while you do the work.
Learn moreNext step
Encrypted messaging that gates itself. The gate is the architecture.
Most practices replace email-with-encryption inside the first month. The governance gap closes architecturally.
No contracts. No consultants. Starting at $39/mo.
