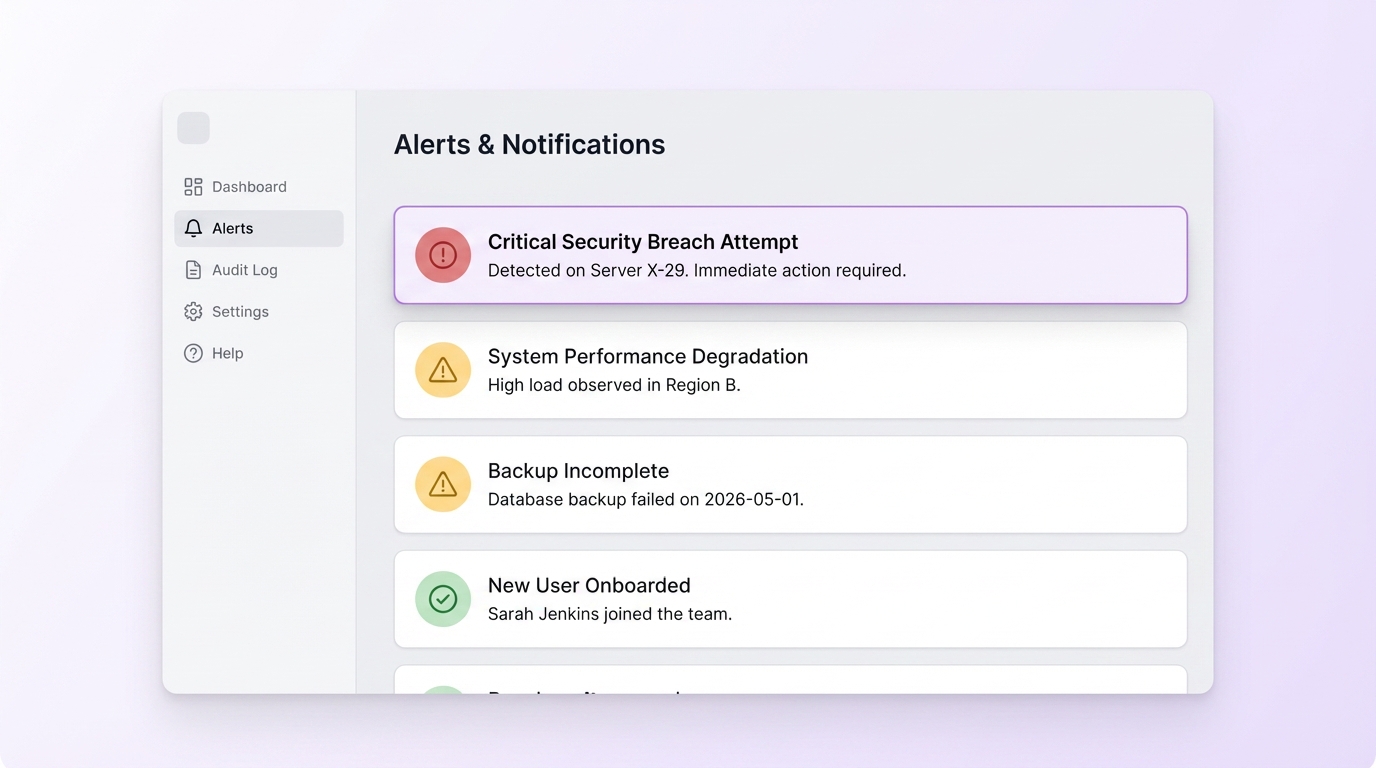
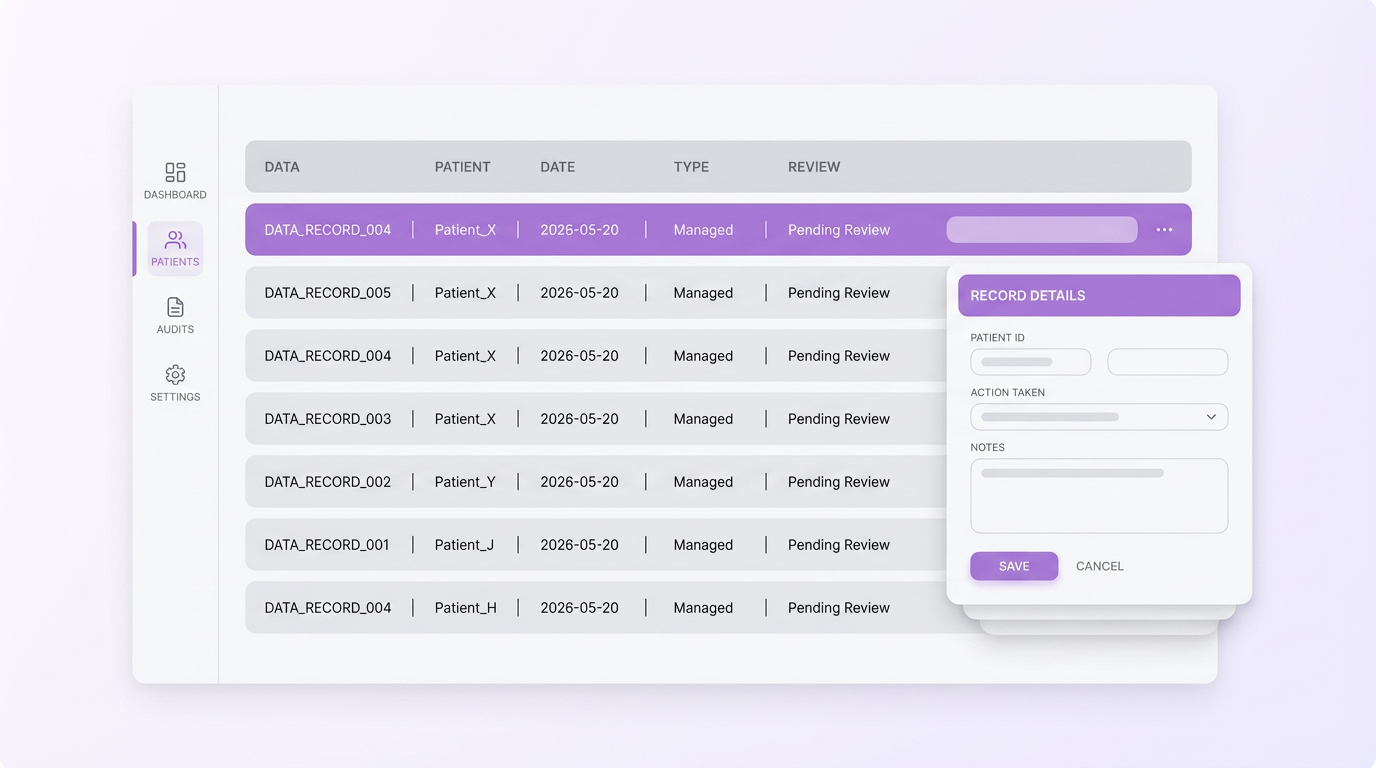
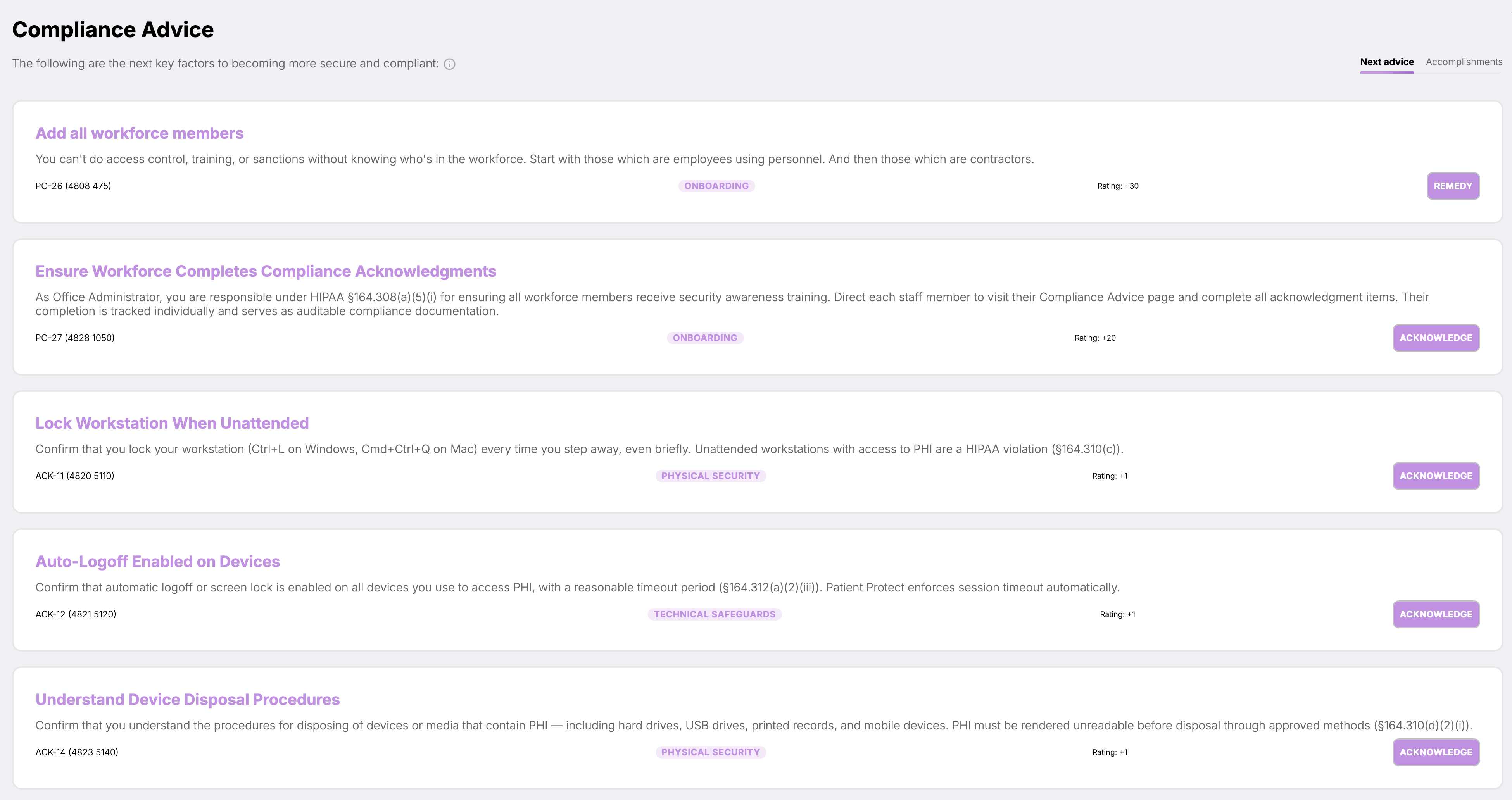
What features does Patient Protect include?
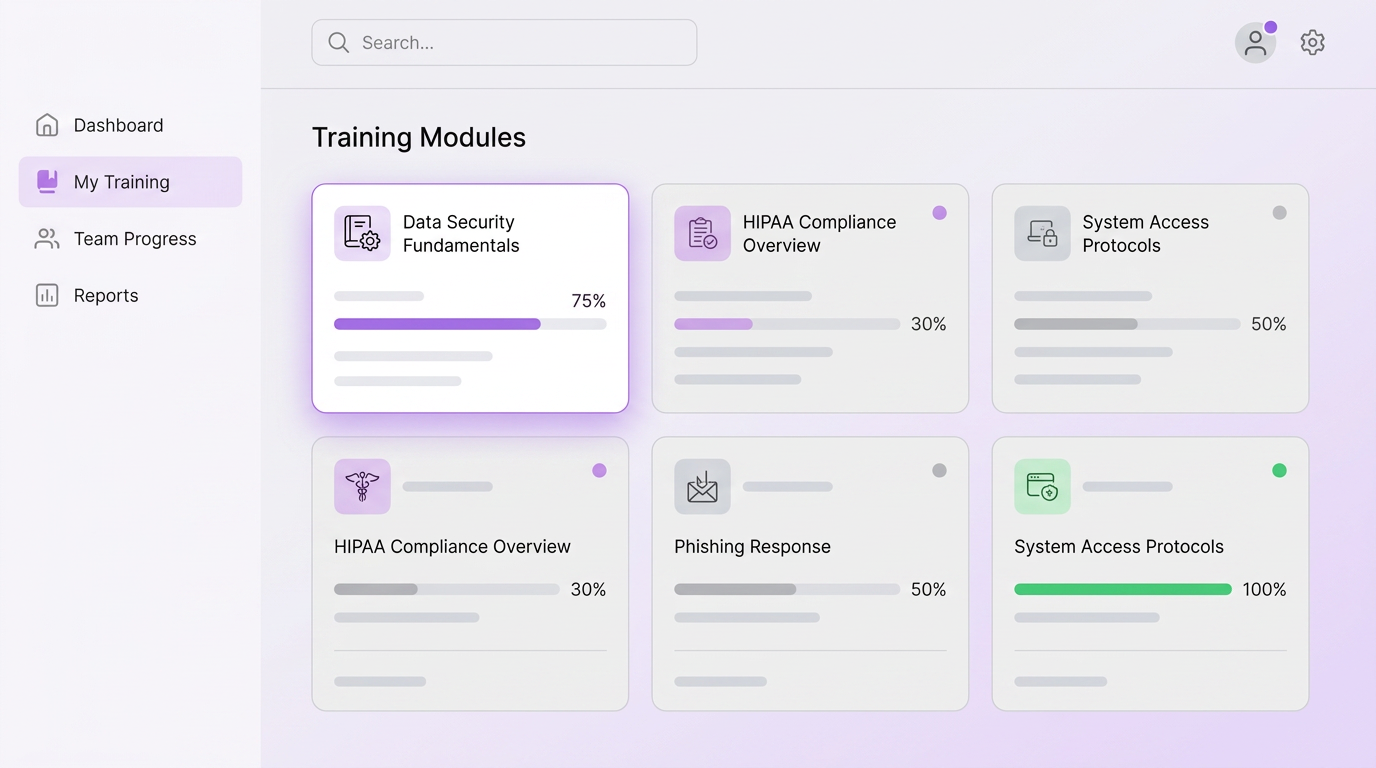
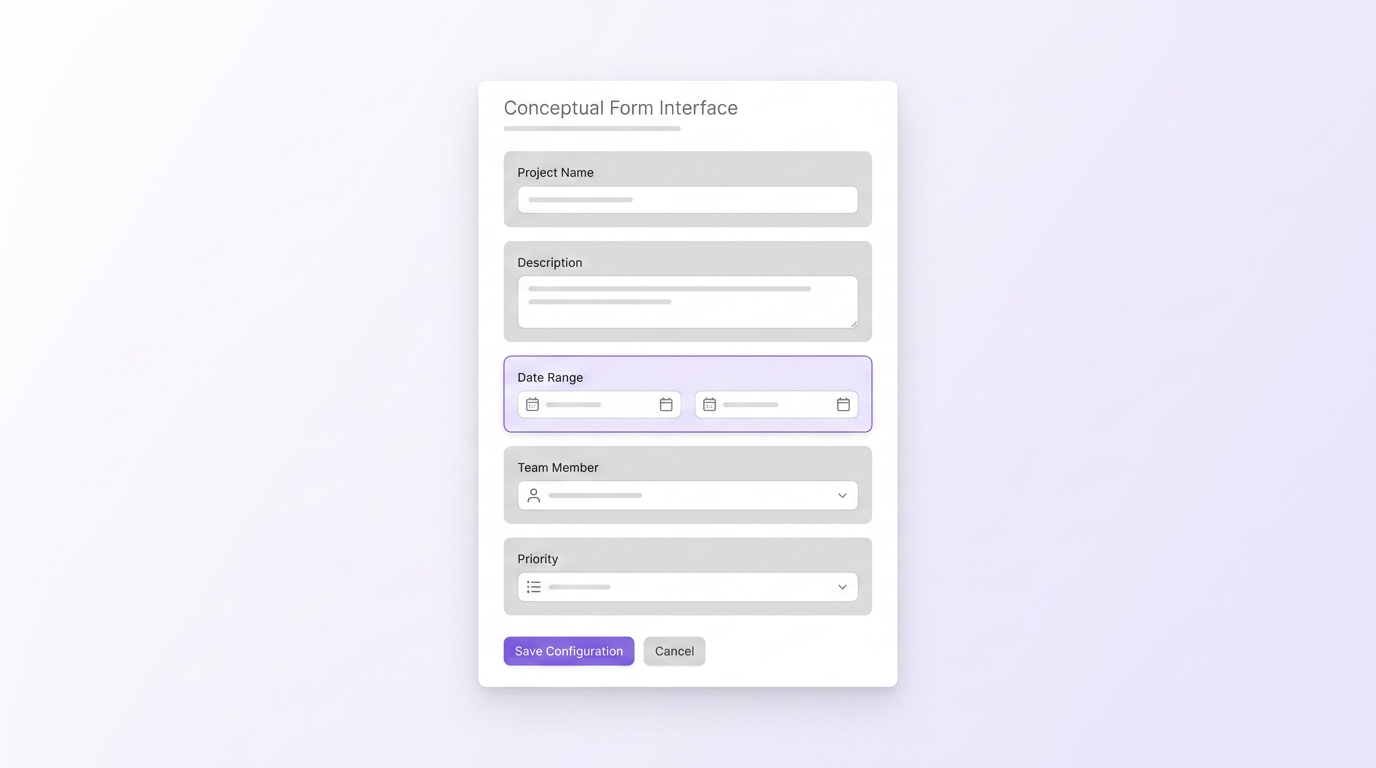
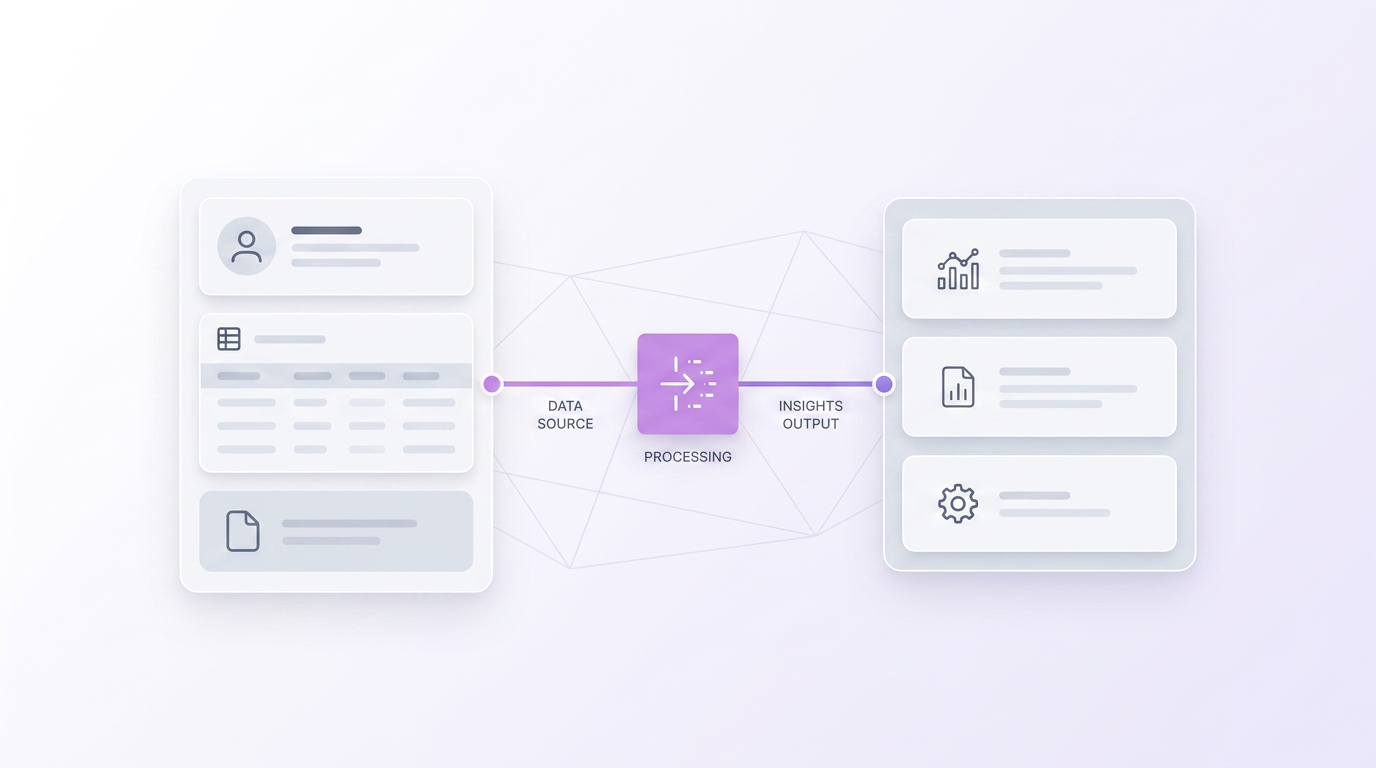
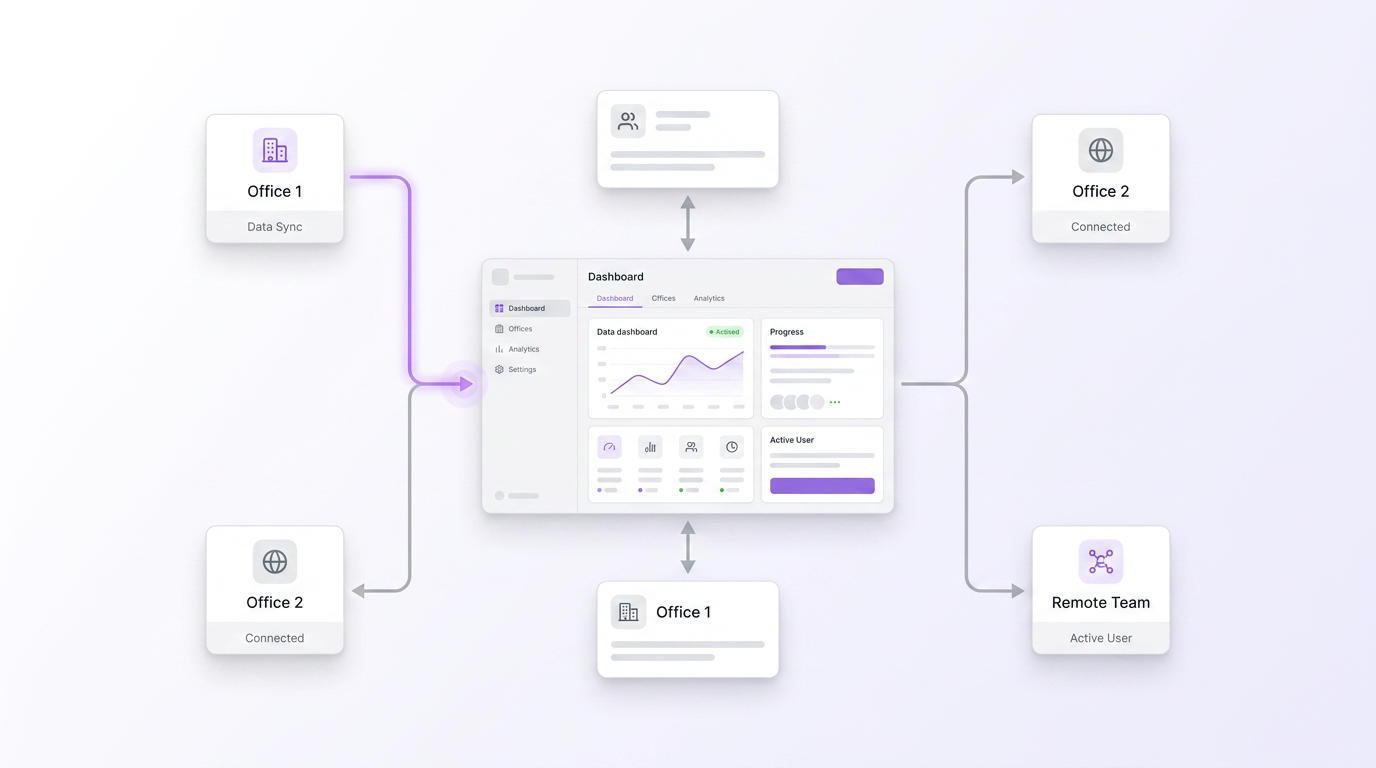
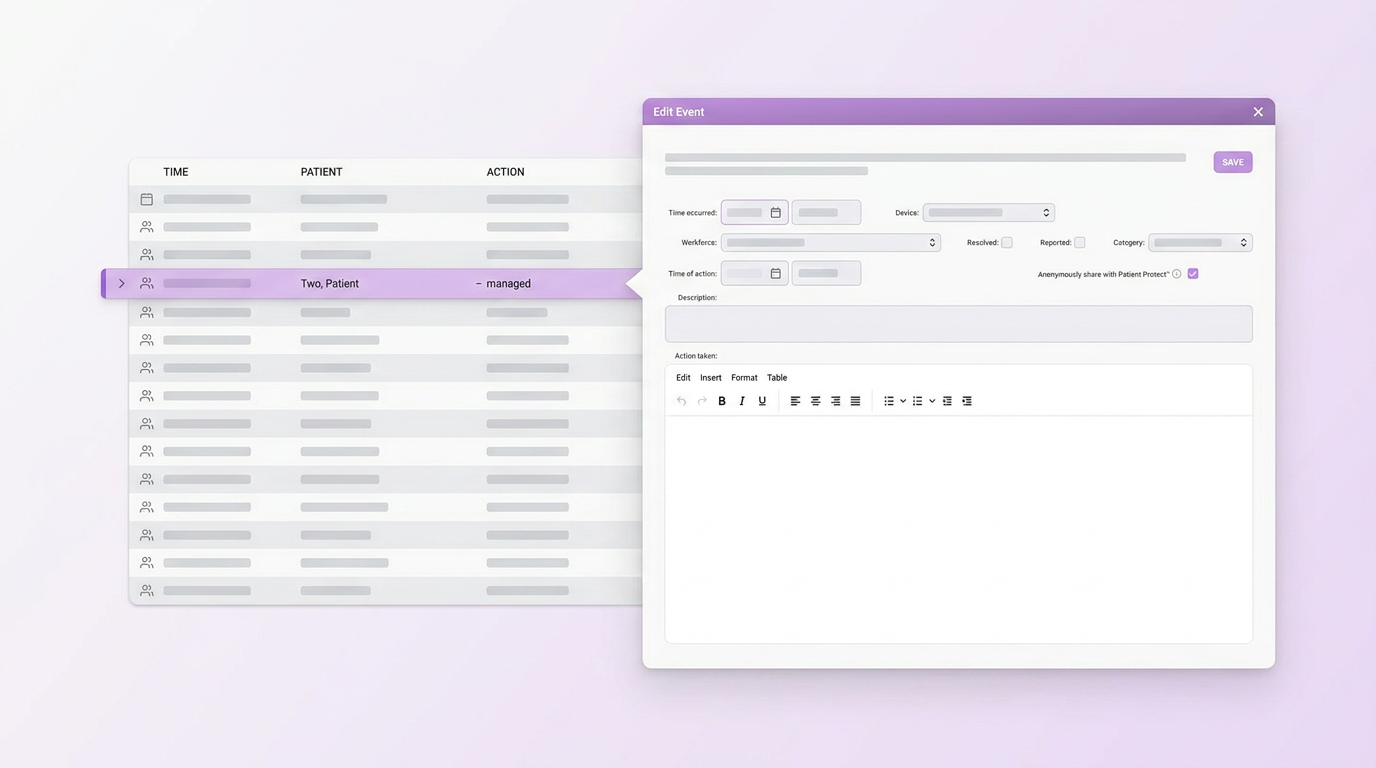
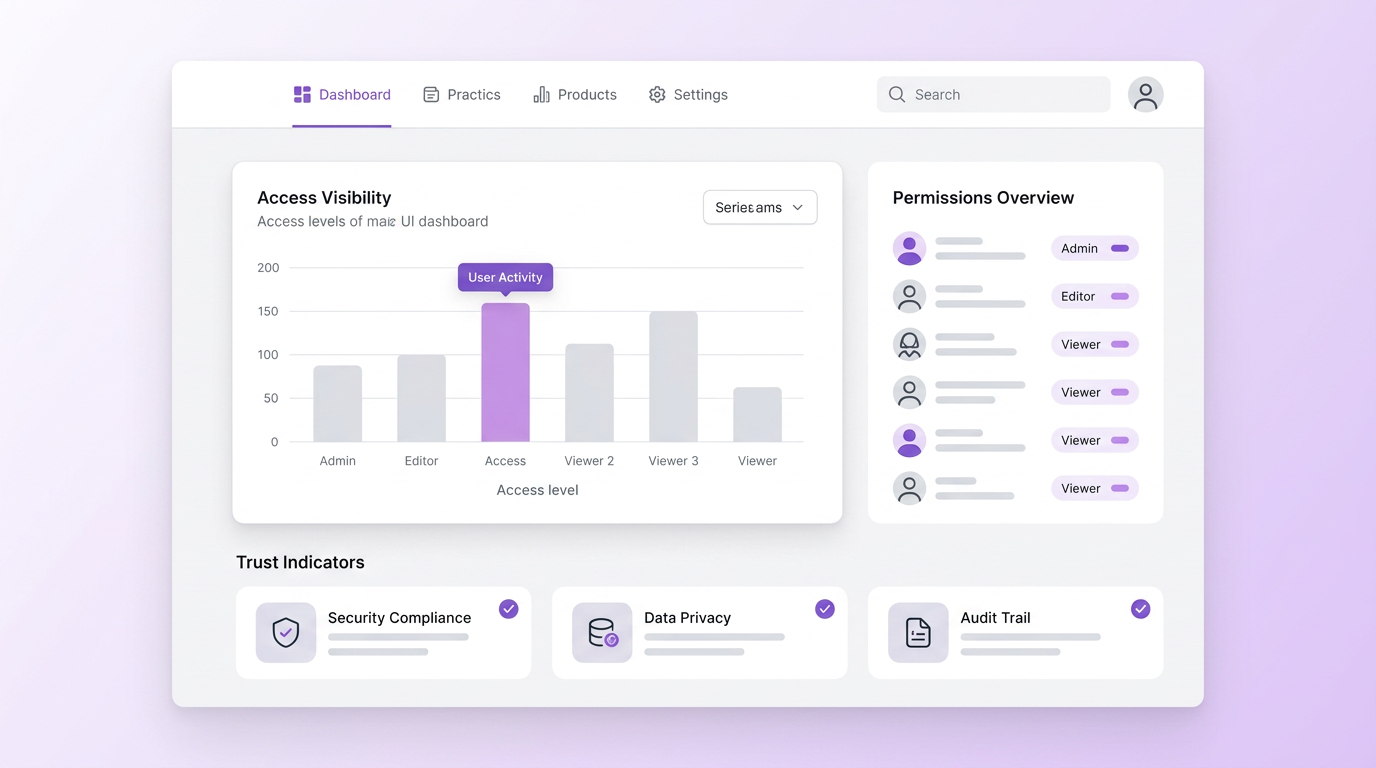
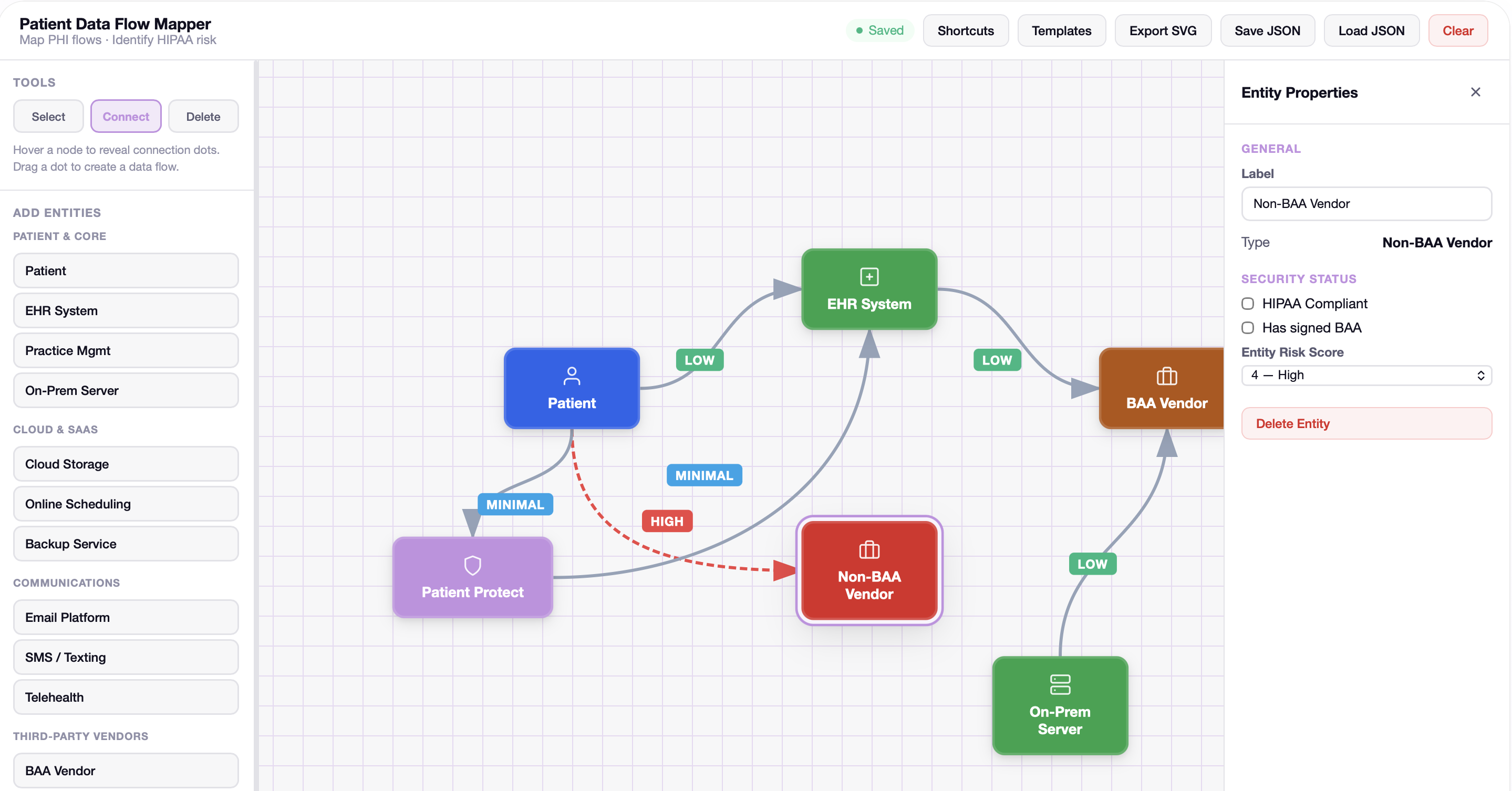
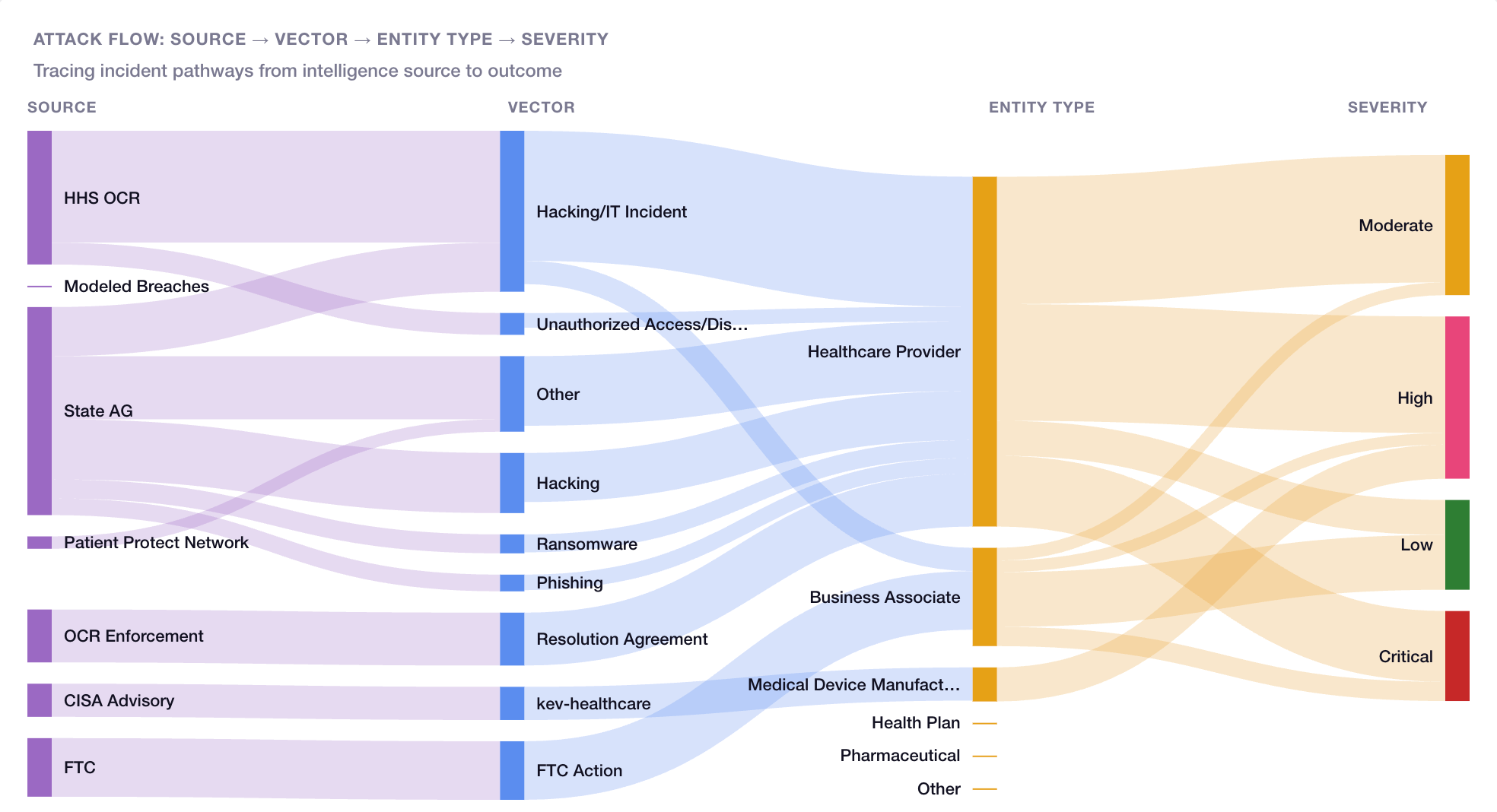
Twenty integrated modules across five layers — System, Defense, Operations, Network, and Intelligence. Core includes 14 modules at $39/month. Pro unlocks all 20 with unlimited AI and expanded training at $99/month.