Defense · Security Alerts
Security alerts that mean something.
Every alert maps to a specific compliance gap. You know what changed, what's at risk, and what to do — immediately.
HIPAA mapping
What this satisfies in the Security Rule.
3 citations, each with the specific Security Alerts behavior that satisfies it. The mapping is the receipt — what you can show an auditor without assembling anything new.
§164.308(a)(1)(ii)(D)Information system activity review
Implements procedures to regularly review records of information system activity. Alerts surface review-worthy activity automatically rather than requiring manual log inspection.
§164.308(a)(6)Security incident procedures
Identifies and responds to suspected or known security incidents. Alerts are the identification mechanism; the response workflow is built into the alert itself.
§164.312(b)Audit controls
The alert system reads from the audit log; alerts are themselves logged for the audit trail.
What it does
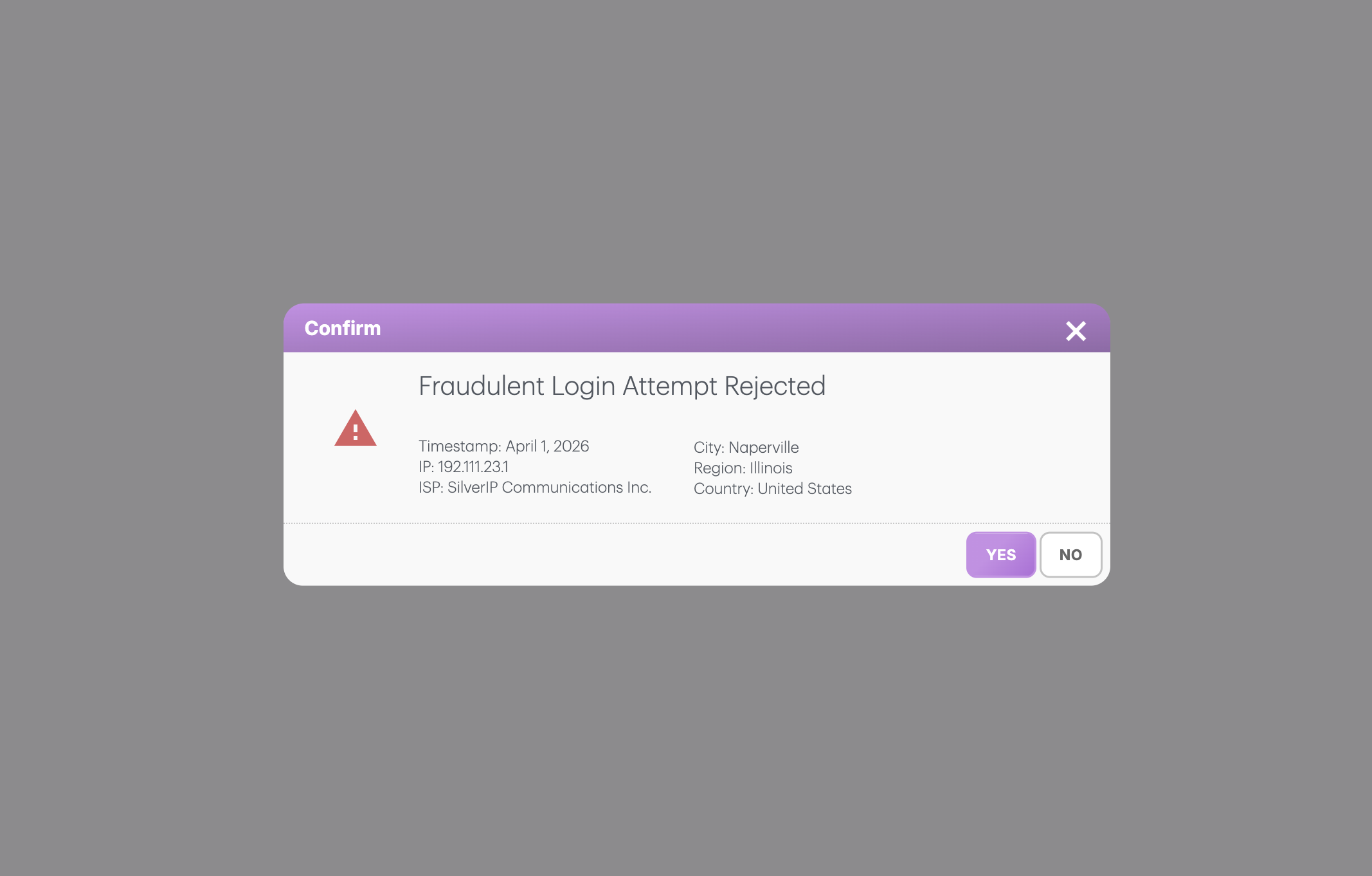
Alerts that tell you what to do, not just that something happened.
Most security tools generate alerts that don't mean anything to the practice. Threat actor names without context. CVE numbers without product mapping. Severity ratings disconnected from your workforce, your data, your operational reality.
Patient Protect's alerts are different. Each one anchors to a specific compliance gap or specific platform event in your practice. The alert tells you what changed, who or what is affected, why it matters in HIPAA terms, and the next step. Severity is calibrated to your context — not a generic CVSS score imported from an industry feed.
Alerts route to the right roles. Workforce-related alerts go to the Office Administrator. Audit anomalies go to the Security Officer. Vendor BAA alerts go to whoever manages the vendor relationship. The right person sees the alert; the wrong person doesn't see noise.
How it works
6 mechanisms keep Security Alerts working.
Compliance-anchored severity.
Severity comes from the compliance impact, not generic CVSS. A vendor BAA hitting Expired is High because messaging is now gated and ePHI exchange is technically prohibited. A workstation running outdated firmware is Medium. A workforce member completing training one day late is Low. The severity is what the practice needs to act on.
Specific to your configuration.
Alerts read from your live platform state. A “missing BAA” alert fires only for vendors you actually have. A “training overdue” alert references your specific cadence settings. A “new browser” alert respects your fingerprinting policy. The alert is about your practice, not industry-generic warnings.
One-click investigation paths.
Every alert links to the underlying records — the audit log entries that triggered it, the workforce member involved, the device or vendor in question, the relevant policy. Investigation that would otherwise require navigating five surfaces happens in one click.
Resolution that closes the loop.
Alerts can be resolved from within the alert itself. Confirm legitimate behavior, escalate to incident, lock an account, adjust a setting — actions are inline. Resolution feeds back into the alert system; repeated patterns inform alert tuning.
Anomaly detection on the audit log.
The platform watches the Personnel ePHI Audit for unusual patterns — access volumes outside the workforce member's normal band, off-hours activity, access to records outside their typical patient panel. Anomalies surface as alerts with the underlying log entries pre-loaded for investigation.
Vendor signal integration.
When a connected vendor reports an incident affecting their own systems, alerts notify your office. The alert includes the scope of potential exposure and the relevant BAA — useful when the question is “do we need to do anything?”
Who this is for
Built for the practices that need it most.
Practices without a dedicated SOC.
Most independent practices don't have a security operations team. Security Alerts gives a single workforce member the operational picture they need to handle the alert volume of a typical practice without becoming a full-time security analyst.
Practices that have ignored security feeds in the past.
Generic threat feeds get tuned out fast. Compliance-anchored alerts stay relevant because they're tied to actual gaps in your specific configuration.
Practices recovering from an incident.
Post-incident, alert sensitivity often gets dialed up. The platform's alert tuning supports temporary elevated sensitivity during recovery periods, with the option to roll back to baseline once the incident is closed.
Connected to
No module is an island.
Security Alertsworks because it's connected. Every signal feeds another module; every closure becomes evidence somewhere else.
Defense layer
ePHI Audit Logs
Anomaly detection in the audit feeds the alert stream; alert events feed back into the audit.
Learn moreDefense layer
Vendor Risk Scanner
Vendor risk events trigger alerts when material; BAA state changes feed alert priority.
Learn moreDefense layer
Breach Simulator
Alert patterns can be tested against simulated attack scenarios; simulation findings configure alert sensitivity.
Learn moreWhat you get
6outcomes you'll feel in week one.
No alert noise.
Compliance-anchored severity means alerts that matter, not alerts that drown the meaningful ones.
Operational context.
Every alert tells you who, what, why, and what to do.
Right person, right alert.
Routing by role; no one sees alerts they can't act on.
One-click investigation.
Linked records load with the alert; no five-tab archaeology.
Inline resolution.
Confirm, escalate, or remediate from the alert itself.
Anomaly detection on the audit.
Patterns get caught that manual review would miss.
How is severity calibrated?
What if we get too many alerts?
Can alerts be muted?
Are alerts sent by email and SMS?
Do alerts integrate with our existing security tools?
Can I see alert history?
Continue exploring
Related features in the platform.
Defense
ePHI Audit Logs
Immutable per-session, per-tab audit trail. OCR-ready by default. No assembly required when the auditor calls.
Learn moreDefense
Vendor Risk Scanner
Evaluates every business associate against your current standing. The vendor risk picture stays current as your BAAs and their behavior do.
Learn moreDefense
Breach Simulator
Run real attack scenarios against your real configuration. The simulator shows where a phishing event, ransomware, or insider threat would land — given your actual controls and gaps.
Learn moreNext step
Alerts that tell you something. With the next step already loaded.
Most practices tune their alert cadence in the first 30 days. After that, the queue stays manageable while the meaningful signals stay sharp.
No contracts. No consultants. Starting at $39/mo.
