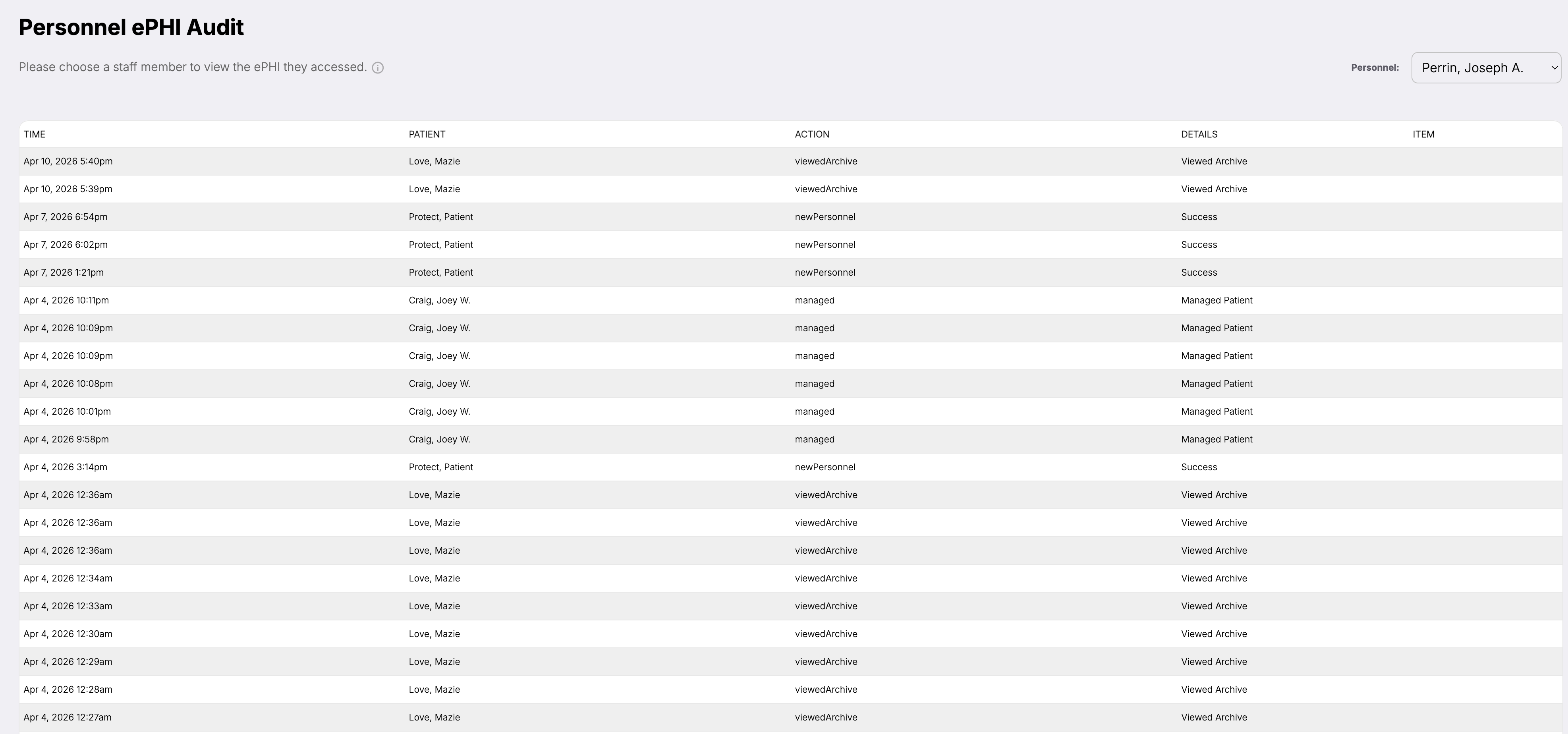
Defense · ePHI Audit Logs
Every access logged. Every action timestamped.
Immutable per-session, per-tab audit trail. OCR-ready by default. No assembly required when the auditor calls.
HIPAA mapping
What this satisfies in the Security Rule.
4 citations, each with the specific ePHI Audit Logs behavior that satisfies it. The mapping is the receipt — what you can show an auditor without assembling anything new.
§164.312(b)Audit controls
Implements hardware, software, and procedural mechanisms that record and examine activity in information systems containing PHI. Patient Protect records every PHI access by every workforce member.
§164.308(a)(1)(ii)(D)Information system activity review
Implements procedures to regularly review records of information system activity. The audit log is searchable, filterable, and reviewable in seconds.
§164.316(b)(2)Time limit
Retains documentation for six years from creation or last effective date. The log retains the full required window automatically.
§164.530(j)Documentation retention
Same six-year requirement applied to privacy documentation. Same compliance posture.
What it does
The audit trail that's already there when the auditor calls.
§164.312(b) is one sentence: implement hardware, software, and procedural mechanisms that record and examine activity in information systems containing electronic protected health information.
Most practices treat that sentence as a problem to be solved the week before audit. Patient Protect treats it as an architectural default — every PHI access, by every workforce member, on every device, is recorded the moment it happens, in a form OCR auditors expect to receive.
When OCR asks who accessed what and when — a question that follows almost every breach notification and many enforcement actions — the answer is one query away. The export is in the format OCR expects. No retroactive log assembly. No “we'll need a few weeks to get back to you.”
How it works
5 mechanisms keep ePHI Audit Logs working.
Per-session, per-tab granularity.
Every authenticated session gets a session ID. Every tab gets a tab ID. Every event records both. Two clinicians on the same device, in the same office, accessing different patients at the same time — distinguishable in the log.
Immutable storage.
Logs are append-only. New entries write; existing entries cannot be modified or deleted. The immutability is enforced at the database layer, not the application layer — application exploits cannot rewrite history. Hash chains validate integrity over time.
PHI scope per event.
Each event records what PHI was accessed at what scope — demographic only, full clinical record, billing record, imaging, etc. When the question is “did this user see clinical notes or just demographics?” the log answers specifically.
Anomaly detection.
Patterns that suggest abnormal access surface as alerts: unusual access times, access volumes outside the member's normal pattern, access to records outside their typical patient panel. Alerts are triaged in the platform with one click to investigate the underlying log entries.
Export in OCR format.
The log exports as CSV, PDF, and as an audit-pack ZIP. The audit pack includes the log itself plus the supporting context — workforce members, roles at the time, devices in service, BAAs active. Audit responses go from “get back to you in a month” to “here by end of day.”
Who this is for
Built for the practices that need it most.
Practices that have to be ready, not get ready.
Audits don't announce themselves with months of warning. The practices that survive enforcement scrutiny are the ones whose audit trail was already there when the request came in. The log is built for that posture.
Specialty practices with high-sensitivity records.
Behavioral health, substance use treatment, HIV care, reproductive health — sectors where access scrutiny is particularly intense. The per-event PHI scope and the anomaly detection are designed for environments where unauthorized access would be a serious matter.
Practices recovering from a breach.
If your practice is in the post-breach corrective action phase, the log is the documentation that demonstrates new control effectiveness. OCR's expectation of “evidence of ongoing audit control function” maps directly to the log's output.
Connected to
No module is an island.
ePHI Audit Logsworks because it's connected. Every signal feeds another module; every closure becomes evidence somewhere else.
Intelligence layer
Audit Replay Timeline
Replay any compliance event from start to finish using the log as source data.
Learn moreOperations layer
Access Management
Every role-permission decision gets recorded in the log; the log validates that access controls actually held.
Learn moreDefense layer
Security Alerts
Anomaly detection in the log feeds the security alert stream.
Learn moreWhat you get
5outcomes you'll feel in week one.
No assembly when audits hit.
The log is already in the format OCR expects. Export and respond.
Per-session, per-tab granularity.
Distinguishable activity even in multi-clinician, multi-tab environments.
Immutable record.
No one can rewrite the audit trail — not workforce, not administrators, not Patient Protect.
Six-year retention by default.
§164.316(b)(2) handled architecturally, not by reminder.
Anomaly surfacing.
The log isn't just storage — it's observation, with patterns that suggest unauthorized access flagged for review.
How long are logs retained?
Can administrators delete log entries?
What about scale? Does the log slow the platform down?
Can I see the log for a specific patient?
Can I see the log for a specific workforce member?
How is this different from just having access logs in my EHR?
Continue exploring
Related features in the platform.
Intelligence
Audit Replay Timeline
Reconstruct what happened, when, in what order, by whom. Every incident investigation, audit response, and forensic exercise — answered from timestamped evidence.
Learn moreOperations
Access Management
From administrator to patient, every role has defined boundaries enforced at every endpoint. No shared logins. No manual overrides.
Learn moreDefense
Security Alerts
Every alert maps to a specific compliance gap. You know what changed, what's at risk, and what to do — immediately.
Learn moreNext step
Audit-readiness is built in. Not built up.
The practices that have audit-ready logs built it in from the start. Patient Protect builds it in for you.
No contracts. No consultants. Starting at $39/mo.
