Defense · Breach Simulator
Find your weakest point. Before someone else does.
Run real attack scenarios against your real configuration. The simulator shows where a phishing event, ransomware, or insider threat would land — given your actual controls and gaps.
HIPAA mapping
What this satisfies in the Security Rule.
3 citations, each with the specific Breach Simulator behavior that satisfies it. The mapping is the receipt — what you can show an auditor without assembling anything new.
§164.308(a)(1)(ii)(A)Risk analysis
Identifies potential risks and vulnerabilities to ePHI confidentiality, integrity, and availability — using your actual configuration rather than generic threat models.
§164.308(a)(1)(ii)(B)Risk management
Implements security measures sufficient to reduce risks. The simulator's output is a prioritized list of those measures, ranked by attack-scenario impact.
§164.308(a)(8)Evaluation
Tests safeguards against realistic scenarios. Each simulator run produces evaluation documentation.
What it does
Real scenarios. Real configuration. Real weakest links.
Generic breach training shows attack patterns against generic companies. Useful for awareness; useless for prioritization. Your practice has specific vendors, specific workforce, specific devices, specific ePHI flows. The attack that lands at a typical hospital is not the attack that would land at your independent behavioral health office.
The Breach Simulator runs scenarios against your actual configuration. It reads your workforce roster, your device inventory, your BAA portfolio, your PHI flow map, and your training completion patterns. It then walks through specific attack scenarios — phishing campaign, lost device, ransomware event, insider misuse — and shows you where the attack would succeed and where it would be stopped.
The output is the weakest link. Where in the sequence would the attack succeed? Which control, if hardened, would have stopped it? The simulator turns abstract risk analysis into specific remediation. “Train workforce” becomes “train these specific 4 workforce members on phishing” because the simulation showed exactly which members the attack would target and which lack current training.
How it works
6 mechanisms keep Breach Simulator working.
Scenario library tuned for independent practices.
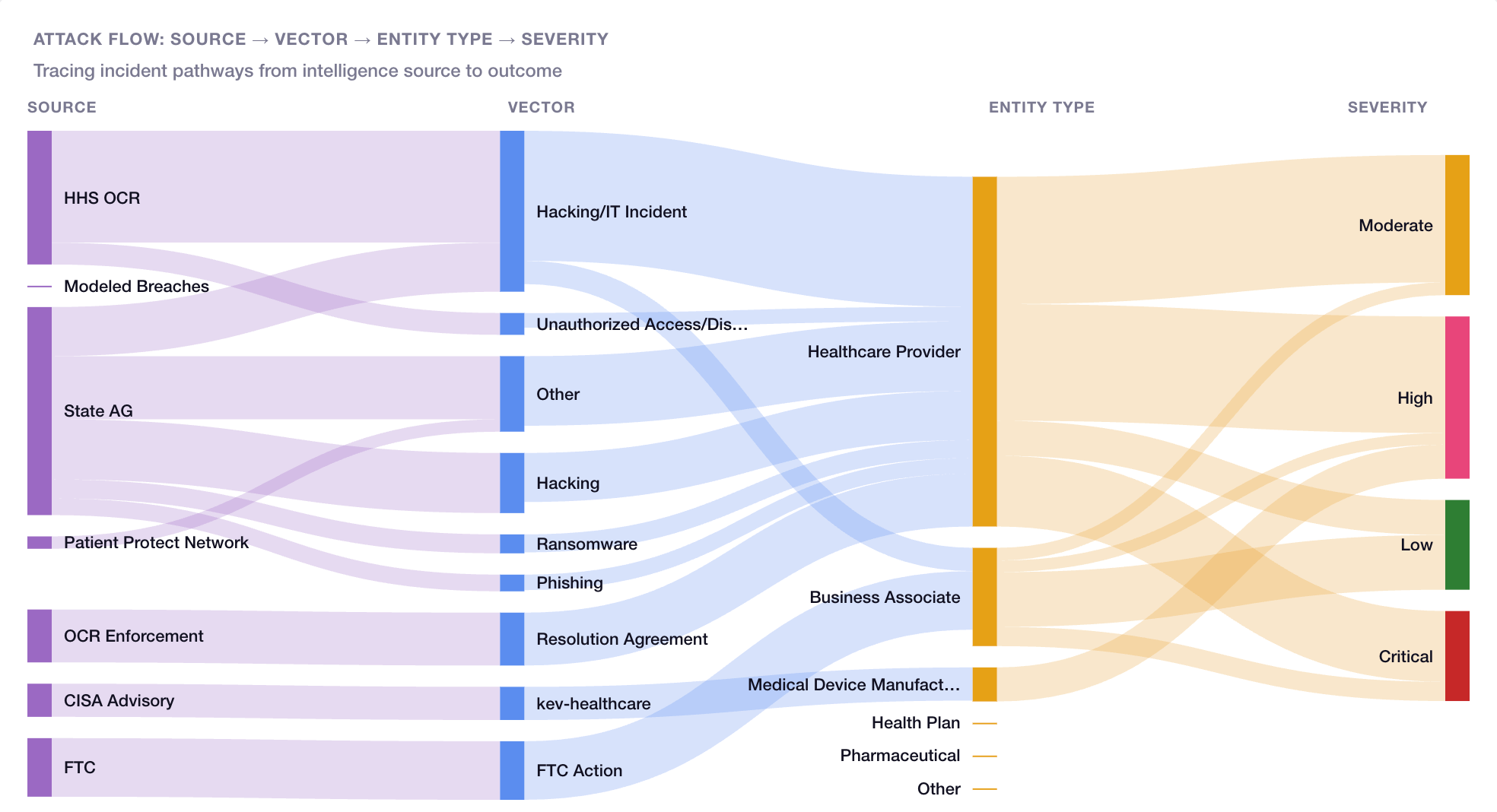
The library covers attacks documented in OCR enforcement actions and HHS breach reports — phishing campaigns, BEC, ransomware via compromised vendors, lost-device events, insider threats during workforce transitions, social engineering targeting clinical staff. Scenarios are updated as threat patterns evolve.
Step-by-step traversal of your configuration.
Each scenario has steps; each step queries platform state. A phishing scenario step asks: “Workforce member receives phishing email. Do they recognize and report it?” The platform checks training completion for the workforce member, prior phishing-test performance, and active alerting. Step succeeds or fails based on actual data.
Weakest-link identification.
The simulation traces to the first failed defensive step. That step is your weakest link for that scenario. Multiple scenarios typically converge on a small set of weakest links — the remediation list is finite and prioritized.
Per-scenario impact modeling.
Each scenario has an estimated impact if successful — record count compromised, regulatory penalty range, notification obligations, recovery time. Impact estimates use industry data calibrated for practice size and sector.
Output integration with the platform.
Simulation outputs feed directly into Compliance Advice and the Autonomous Compliance Engine. “Weakest link: phishing training for these 4 workforce members” becomes a concrete task in the queue, not a finding lost in a PDF.
Re-runs as your configuration changes.
Run the same scenario before and after remediation to verify the weakest link has moved. The simulator confirms the work actually closed the gap.
Who this is for
Built for the practices that need it most.
Practices that want their training to be specific.
Generic phishing training reaches everyone equally and produces generic results. Simulation-targeted training reaches the specific workforce members an actual attack would target.
Practices that have done a checklist SRA but want more.
A checklist SRA produces a list of administrative gaps. Scenario simulation produces a list of operational gaps that actually lead to compromise — different list, more actionable.
Practices preparing for board or insurance reviews.
Boards and insurance underwriters increasingly ask “have you tested your controls?” Generic training records satisfy this weakly. Scenario simulation produces specific evidence — “these scenarios were run on these dates with these outcomes” — that lands well with both audiences.
Practices in sectors with sector-specific threats.
Behavioral health attacks differ from optometry attacks differ from primary care attacks. Sector-specific scenarios in the library calibrate the simulation to the realistic threats for your sector.
Connected to
No module is an island.
Breach Simulatorworks because it's connected. Every signal feeds another module; every closure becomes evidence somewhere else.
Intelligence layer
Data Flow Mapper
PHI flow paths feed scenario step-by-step traversal; the simulator knows where data actually moves.
Learn moreIntelligence layer
Financial Exposure Tracker
Scenario impact estimates feed the financial exposure model.
Learn moreDefense layer
Security Alerts
Simulation findings can configure alert sensitivity for the specific patterns the simulation identified.
Learn moreWhat you get
6outcomes you'll feel in week one.
Specific weakest links.
Not “phishing risk exists” — “these 4 workforce members are the weakest link in the phishing scenario.”
Prioritized remediation.
Multiple scenarios converge on a finite list of high-impact gaps.
Sector-specific scenarios.
Your sector's actual threat patterns, not industry-generic.
Audit-defensible evaluation.
Documented simulation runs satisfy §164.308(a)(8) directly.
Training that matters.
Trains the specific people the specific attacks would target.
Re-run verification.
Confirm remediation actually closed the gap.
Is this an actual attack against our systems?
Can we add custom scenarios?
How often should we run scenarios?
Are the scenarios based on real attacks?
What does scenario impact actually mean?
Is this Pro-only?
Continue exploring
Related features in the platform.
Intelligence
Data Flow Mapper
Visual map of every place PHI flows in your practice. Vendors. Systems. Workforce. Find concentration risk before it concentrates into a breach.
Learn moreIntelligence
Financial Exposure Tracker
Models penalty exposure from your specific gaps against actual enforcement patterns. Compliance translated into the language boards and owners actually plan around.
Learn moreDefense
Security Alerts
Every alert maps to a specific compliance gap. You know what changed, what's at risk, and what to do — immediately.
Learn moreNext step
Find what would actually land. Fix it before it does.
Most practices run their first scenario inside week one. The weakest links surface fast — and so does the remediation list.
No contracts. No consultants. Starting at $99/mo.
