Intelligence · Financial Exposure Tracker
What your compliance gaps would cost. In dollars.
Models penalty exposure from your specific gaps against actual enforcement patterns. Compliance translated into the language boards and owners actually plan around.
HIPAA mapping
What this satisfies in the Security Rule.
3 citations, each with the specific Financial Exposure Tracker behavior that satisfies it. The mapping is the receipt — what you can show an auditor without assembling anything new.
§164.308(a)(8)Evaluation
Performs periodic evaluations of security safeguards. Financial modeling is a sophisticated form of evaluation that quantifies the consequence of unaddressed gaps.
§164.404Notification to individuals
Specifies notification requirements for breaches. Notification cost is one input in the exposure model.
§164.408Notification to the Secretary
Specifies reporting obligations. The Tracker accounts for the 500-record threshold and its enforcement implications.
What it does
Compliance, in the language leadership actually plans around.
Compliance reports speak the language of citations and controls. Boards speak the language of dollars. The translation is typically left to the practice owner — “we have N gaps, what does that mean for the practice if something goes wrong?” — and is typically done badly. The result is compliance that's underfunded by leadership who can't see the financial reality of the gaps.
The Financial Exposure Tracker does the translation. It reads your live compliance state, your data flow map, your vendor relationships, and your record volume. It models penalty exposure against actual OCR enforcement patterns, breach-cost data from peer-reviewed research, and your practice's specific parameters.
The Tracker isn't fortune-telling. The exposure isn't what will happen; it's what reasonable financial modeling would estimate is at stake. The number moves down as you close gaps — the practice that closed five high-risk findings sees exposure reduce by the modeled penalty value of those findings. The reduction is real motivation to do the work.
How it works
6 mechanisms keep Financial Exposure Tracker working.
OCR enforcement pattern calibration.
The Tracker maintains a database of OCR enforcement actions — settled cases, civil money penalties, corrective action plans — analyzed by gap type, practice size, and outcome. New enforcement actions are added as they're announced; the model re-calibrates against fresh data.
Per-gap exposure mapping.
Each open gap on your platform maps to one or more enforcement patterns. An expired BAA with a vendor that handles ePHI maps to §164.308(b)(1) enforcement patterns; the average settlement in those patterns informs the gap's exposure value.
Practice-specific parameters.
Record count is the most significant per-practice variable because it drives notification cost and the breach-size threshold. Sector matters (behavioral health enforcement patterns differ from primary care). Prior enforcement history matters (practices with prior issues see uplift in subsequent exposure).
Layered exposure modeling.
Total exposure breaks into layers: regulatory penalty (OCR fines), notification cost (per-record contacted), incident response cost (forensics, legal, recovery), and reputational impact (where quantifiable through patient-attrition modeling). Each layer has its own model and its own range.
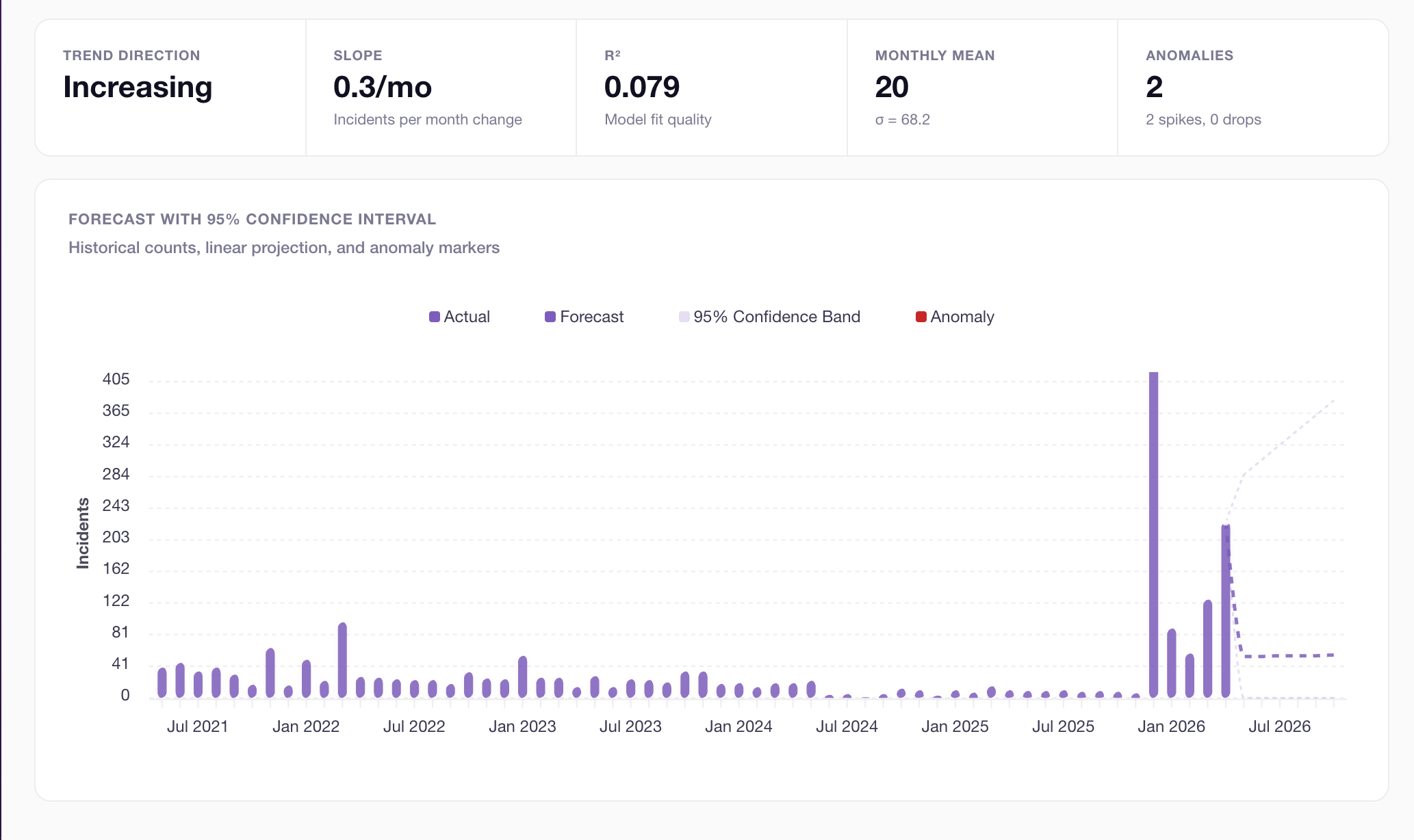
Trend over time.
Exposure trend graph shows movement as gaps close or open. The graph is part of the conversation with leadership: “we reduced modeled exposure by $X since the last review.”
Sensitivity analysis.
Adjust assumptions and see exposure response. What if our record count grew 20%? What if a specific high-risk vendor were replaced? What if all open Advice items were closed? The model accommodates the analysis.
Who this is for
Built for the practices that need it most.
Practice owners and operators with budget authority.
Compliance budget conversations are stuck without dollar context. The Tracker is the dollar context — “this $X investment in remediation reduces modeled exposure by $Y.”
Practices preparing for board or investor review.
Boards expect financial modeling. Practice acquirers and investors do too. The Tracker is the artifact that shows compliance in financial terms — far more credible than narrative descriptions of compliance status.
Practices with cyber insurance considerations.
Cyber insurers increasingly want to see modeled exposure during underwriting. Practices using the Tracker can present underwriters with structured exposure analysis — typically favorable to underwriting outcomes.
Practices in growth or transition.
Acquisitions, expansions, and mergers all bring inherited compliance state. The Tracker quantifies the financial implications of inherited gaps — useful in transaction diligence and post-transaction prioritization.
Connected to
No module is an island.
Financial Exposure Trackerworks because it's connected. Every signal feeds another module; every closure becomes evidence somewhere else.
Intelligence layer
Data Flow Mapper
Flow data informs which gaps have which exposure characteristics.
Learn moreDefense layer
Breach Simulator
Scenario impact estimates feed the incident response exposure layer.
Learn moreSystem layer
Risk Intelligence
Current risk state is the primary input; gap closure reduces exposure.
Learn moreWhat you get
6outcomes you'll feel in week one.
Dollar-denominated compliance.
Translation that boards and owners can act on.
Enforcement-calibrated.
Modeling against actual OCR settlement patterns, not hypothetical scenarios.
Practice-specific.
Calibrated by your record volume, sector, and history.
Layered exposure.
Penalty + notification + incident response + reputational, each with its own model.
Trend over time.
Watch exposure reduce as work closes.
Sensitivity analysis.
Adjust assumptions, see response.
How accurate is the modeling?
Why is the exposure so high / so low?
Does this account for cyber insurance?
Can I share the exposure number externally?
What if I disagree with the methodology?
Is this Pro-only?
Continue exploring
Related features in the platform.
Intelligence
Data Flow Mapper
Visual map of every place PHI flows in your practice. Vendors. Systems. Workforce. Find concentration risk before it concentrates into a breach.
Learn moreDefense
Breach Simulator
Run real attack scenarios against your real configuration. The simulator shows where a phishing event, ransomware, or insider threat would land — given your actual controls and gaps.
Learn moreSystem
Risk Intelligence
Risk recalculates the moment a gap closes. Not at quarter-end. Not when you remember to run a report. The picture is always current.
Learn moreNext step
Compliance translated into the language leadership actually plans around.
Most Pro practices model their exposure inside the first week. The trend line begins as soon as gaps close.
No contracts. No consultants. Starting at $99/mo.
