HIPAA Compliance
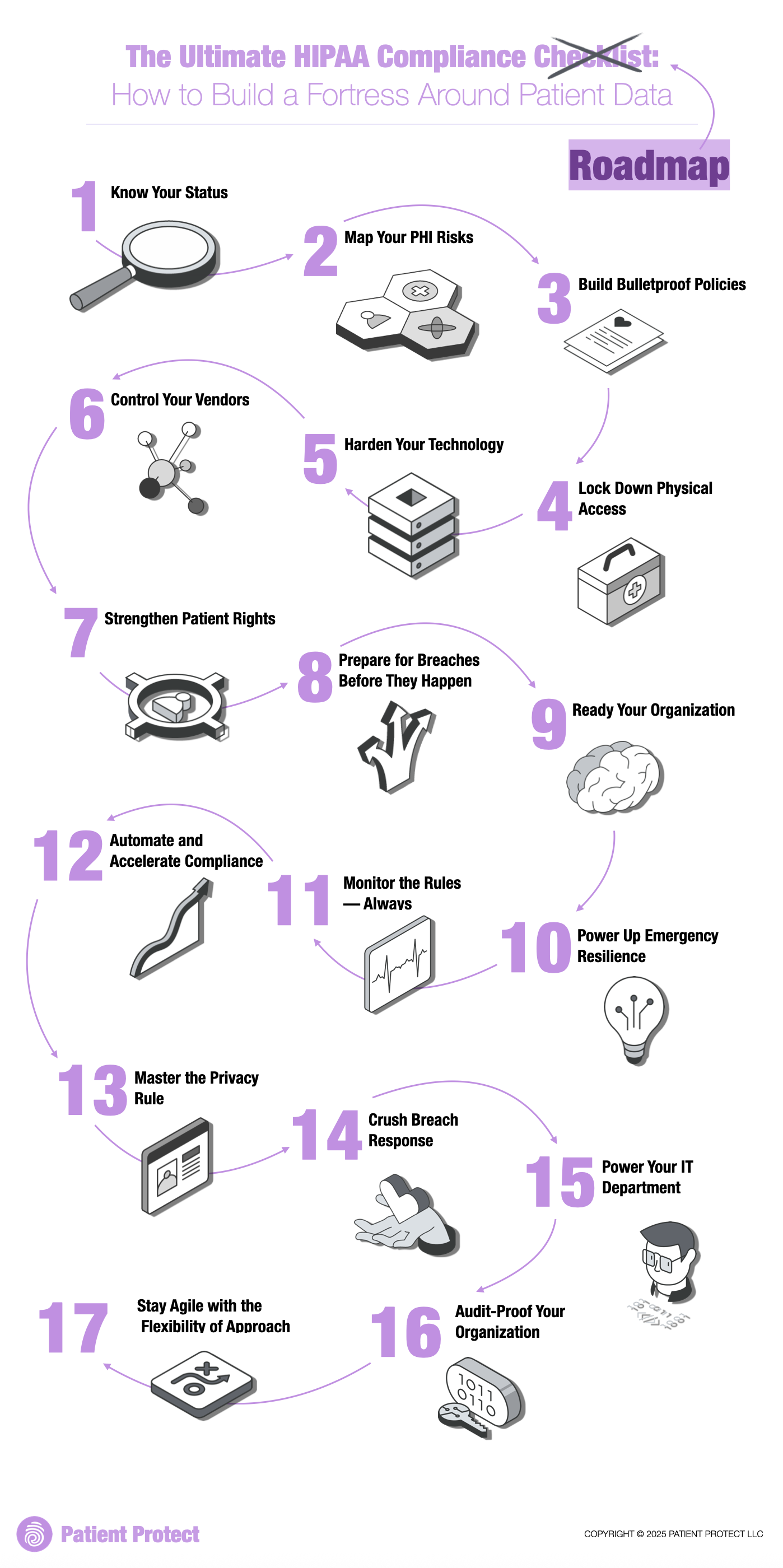
The Ultimate HIPAA Compliance Checklist: 17 Steps That Actually Matter
A 17-step operational framework for HIPAA compliance built for independent healthcare practices. Not a checkbox list — a roadmap from gap identification to audit readiness.

A checklist is not a compliance program — but it is a good starting structure
Most HIPAA compliance checklists fail because they flatten a complex operational problem into a list of yes/no questions. "Do you have an access control policy?" Yes. Is it enforced? Is it current? Does staff know about it? Those questions matter more — and most checklists never ask them.
This framework is organized around three pillars: know your risk, build your controls, and prove your work. Each step has a concrete outcome, not just a box to check.
Pillar 1: Know your risk
1. Conduct a security risk assessment
Identify where PHI exists, how it flows, and what threats apply. This is not optional — it is the single most cited requirement in OCR enforcement actions. The ePHI data flow mapper is a free starting point.
2. Inventory all systems that touch PHI
EHR, billing software, email, cloud storage, patient portal, fax, phones, paper records. If it stores, transmits, or processes PHI, it belongs on this list.
3. Identify all business associates
Every vendor that touches PHI needs a BAA. This includes cloud providers, IT support, billing services, shredding companies, and answering services. If you cannot list them all right now, that is your first gap.
4. Document current threats and vulnerabilities
Not theoretical risks — actual threats relevant to your practice size, specialty, and technology. Ransomware, phishing, unauthorized access, lost devices, and insider threats are the most common for independent practices.
Pillar 2: Build your controls
5. Implement access controls
Unique user IDs for every person who accesses PHI. Role-based permissions so staff only see what they need. Automatic session timeouts. Emergency access procedures.
6. Enable encryption
PHI at rest and in transit should be encrypted. Full-disk encryption on workstations, TLS for email and web traffic, encrypted backups. Encryption is an addressable specification — if you choose not to implement it, document why.
7. Deploy audit controls
Know who accessed what, when, and from where. EHR audit logs are a start. Review them regularly — not just when something goes wrong.
8. Establish password and authentication policies
Minimum complexity requirements. No shared credentials. Multi-factor authentication wherever possible — and soon, likely mandatory under the proposed Security Rule amendments.
9. Secure physical access
Locked server rooms, screen locks at workstations, clean desk policies, visitor logs. Physical security is part of the Security Rule and routinely overlooked.
10. Train your workforce
Every member of the workforce — not just clinical staff — needs HIPAA training at onboarding and at least annually. Document who was trained, when, and on what.
11. Write policies that match reality
Policies should describe how the practice actually operates, not how it aspires to operate. If the written policy says "all workstations lock after 5 minutes" and they do not, the policy creates evidence of non-compliance rather than evidence of compliance.
12. Establish a sanctions policy
The workforce needs to know what happens when policies are violated. Document the sanctions policy and apply it consistently.
Pillar 3: Prove your work
13. Build an incident response plan
Define what constitutes a security incident, who is responsible for what, and how the practice will investigate, contain, and report. The free incident response template provides a starting framework.
14. Know your breach notification obligations
If a breach affects 500+ individuals, HHS must be notified within 60 days and media must be notified. For smaller breaches, an annual log submission to HHS is required. Every affected individual must be notified within 60 days regardless of breach size.
15. Document everything
Risk assessments, training records, policy updates, incident investigations, BAA inventory, remediation actions. If it is not documented, it did not happen — at least as far as OCR is concerned.
16. Review and update regularly
Compliance is not a project with a finish line. Policies, risk assessments, and training should be reviewed whenever operations change — and at minimum annually.
17. Test your readiness
Run a tabletop exercise. Simulate a breach scenario and walk through the response. The first time your team executes the incident response plan should not be during an actual incident.
From checklist to operating system
This framework gives you a sequence. What it cannot give you is continuous enforcement — the daily discipline of keeping each step current as staff change, vendors change, and threats evolve.
That is where a compliance platform becomes valuable. The HIPAA compliance roadmap turns this framework into an interactive guide. Patient Protect turns it into a daily operating system with live scoring, task management, and audit-ready documentation.
