17-Step HIPAA Compliance Series
Build Bulletproof HIPAA Policies — Appoint Officers, Train, and Enforce (Step 3 of 17)
Step 3: Assign Privacy and Security Officers, deliver required training, and document policies to protect your practice and meet HIPAA standards.

Policies are not documentation — they are operational commitments
Most HIPAA violations that reach OCR enforcement share a common trait: the practice had a policy on paper, but the policy did not describe what actually happened on the ground. A written access control policy means nothing if three staff members share the same login. A training policy means nothing if the last training session was two years ago.
This is Step 3 of our 17-step HIPAA compliance roadmap. In Step 1, you determined your HIPAA status. In Step 2, you mapped your risks. Now you build the operational framework — the people, policies, and training — that turns risk findings into daily practice.
Appoint a Privacy Officer and Security Officer
HIPAA requires every Covered Entity to designate a Privacy Officer (45 CFR 164.530(a)(1)) and a Security Officer (45 CFR 164.308(a)(2)). These are not optional roles. They are regulatory requirements with specific responsibilities.
The Privacy Officer is responsible for:
- Developing and implementing privacy policies and procedures
- Handling patient complaints about privacy practices
- Delivering privacy-related training
- Managing the Notice of Privacy Practices
- Overseeing PHI use and disclosure decisions
The Security Officer is responsible for:
- Developing and implementing security policies and procedures
- Conducting and overseeing risk assessments
- Managing security incidents
- Ensuring technical safeguards are in place and functioning
- Monitoring access controls and audit logs
In a small practice — a solo dentist, a three-provider medical office, a behavioral health clinic with a handful of clinicians — the same person can hold both roles. That is explicitly permitted under HIPAA. What is not permitted is having no one designated at all.
The designation must be documented. It does not require a formal job title change or additional compensation, but the individual must know they hold the role, understand the responsibilities, and have the authority to enforce policies.
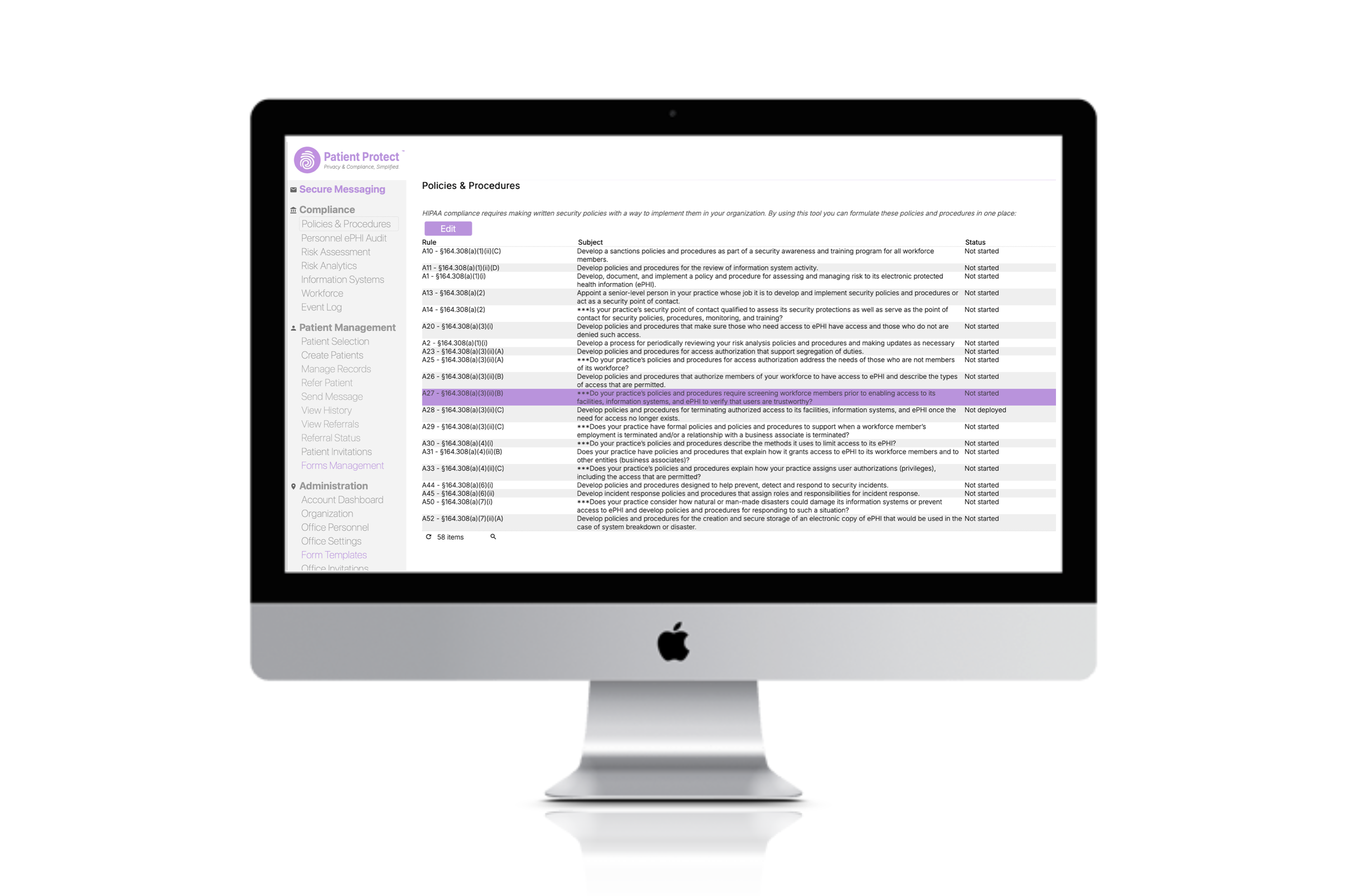
Build policies that match reality
HIPAA requires documented policies and procedures across both the Privacy Rule and the Security Rule. The specific policies you need depend on your practice, but at minimum you should document:
Privacy policies
- Uses and disclosures of PHI (treatment, payment, operations, and all other purposes)
- Patient rights (access, amendment, accounting of disclosures, restrictions)
- Minimum necessary standard (how you limit PHI access to what is needed)
- Notice of Privacy Practices
- Complaint procedures
- Sanctions for policy violations
Security policies
- Access control (unique user IDs, role-based access, emergency access)
- Audit controls (what is logged, how logs are reviewed)
- Integrity controls (how you prevent unauthorized alteration of ePHI)
- Transmission security (encryption, secure messaging)
- Workstation use and security
- Device and media controls (disposal, re-use, movement of devices)
- Facility access controls
- Incident response and breach notification procedures
- Contingency planning (backup, disaster recovery, emergency operations)
- Business associate management
The critical rule: policies must describe reality
If your policy says workstations lock after five minutes of inactivity but they are configured for fifteen, you have created evidence of non-compliance. If your policy says all PHI transmissions are encrypted but staff routinely email unencrypted patient information, your policy is a liability, not a safeguard.
Write policies that describe how your practice actually operates today. Where reality falls short of best practice, document the gap and create a remediation timeline. An honest policy with a documented improvement plan is infinitely stronger than a polished policy that does not match operations.
Train your workforce — all of it
HIPAA requires workforce training at onboarding and periodically thereafter. "Workforce" is broader than you think — it includes employees, volunteers, trainees, and any person whose conduct is under your direct control, whether or not they are paid.
Training must cover:
- Privacy awareness — what PHI is, how it can and cannot be used, patient rights, minimum necessary standard
- Security awareness — password hygiene, phishing recognition, physical security, device security, incident reporting
- Role-specific training — front desk staff need different training than clinicians. The billing team handles different PHI flows than the clinical team.
- Policy-specific training — when policies change, affected workforce members must be retrained on the changes
How often
HIPAA says training must be provided "as necessary and appropriate." In practice, this means:
- At hire — before the new team member accesses any PHI
- Annually — at minimum, to address emerging threats and refresh core concepts
- When policies change — targeted training on the specific changes
- After incidents — if a security event reveals a training gap, address it immediately
We offer free HIPAA training that covers the fundamentals for independent practices.
Document everything
For every training session, record:
- Date of training
- Topics covered
- Attendees (with signatures or electronic acknowledgment)
- Trainer name
- Materials used
This documentation is among the first things OCR requests in an investigation. If you cannot prove training occurred, it did not occur — as far as the regulator is concerned.
Enforce with a sanctions policy
The Privacy Rule at 45 CFR 164.530(e)(1) requires Covered Entities to apply appropriate sanctions against workforce members who violate policies. You need a documented sanctions policy that:
- Defines what constitutes a violation
- Establishes a range of consequences (verbal warning, written warning, suspension, termination)
- Applies consistently across the organization
- Is communicated to all workforce members
The sanctions policy is not about creating a punitive environment. It is about making clear that HIPAA policies are operational requirements, not suggestions. Staff who understand there are consequences for violations are more likely to follow procedures — and more likely to report incidents early, before they escalate.
Common mistakes in this step
Designating officers but not empowering them. A Privacy Officer who cannot enforce policy changes is a figurehead. The designation must come with authority.
Copying template policies without customization. Generic policy templates are a starting point, not a finished product. Your policies must reflect your specific practice environment — your systems, your workflows, your risk profile.
Training once and forgetting. Annual training is the minimum. Threats evolve, staff turns over, and systems change. Training must keep pace.
Failing to document. Undocumented policies, undocumented training, and undocumented officer designations are functionally nonexistent under HIPAA.
Policies are the bridge between risk and action
Step 2 told you where your vulnerabilities are. This step creates the operational framework to address them. The policies you write here, the officers you designate, and the training you deliver become the mechanism through which risk mitigation actually happens.
In the next step, we turn to the physical environment — because ePHI security is not only a digital problem.
Resources
| Resource | Description | |---|---| | HHS Sample Notice of Privacy Practices | Official sample NPP template practices can adapt | | 45 CFR §164.530 (Administrative Requirements) | Official HIPAA regulation requiring written policies, staff training, and officer assignment | | HHS Privacy Rule Summary | Simplified overview of HIPAA Privacy Rule requirements including documentation needs |
This is Step 3 of our 17-step HIPAA compliance roadmap. Previous: Step 2 — Map Your PHI Risks. Next: Step 4 — Lock Down Physical Access to ePHI.
