17-Step HIPAA Compliance Series
Map Your PHI Risks — Master Risk Assessments and Threat Monitoring (Step 2 of 17)
Step 2: Conduct risk assessments, monitor threats, and document mitigation strategies to keep your practice secure and audit-ready.

Risk assessment is not optional — it is the foundation of HIPAA compliance
If there is one requirement OCR cites more than any other in enforcement actions, it is the failure to conduct an adequate risk assessment. Not encryption. Not training. Not breach notification. The risk assessment.
The Security Rule at 45 CFR 164.308(a)(1)(ii)(A) requires every Covered Entity and Business Associate to "conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information."
This is Step 2 of our 17-step HIPAA compliance roadmap because every control you build in Steps 3 through 17 is informed by what you discover here. Without a current risk assessment, you are building compliance in the dark.
What a proper risk assessment actually requires
A HIPAA risk assessment is not a checklist and it is not a questionnaire. It is a structured analysis of your specific environment. Here is what it must include:
Identify where ePHI lives
Every system, device, application, and workflow that stores, processes, or transmits electronic protected health information. This includes:
- Your EHR and practice management system
- Email (including personal email staff may use)
- Cloud storage services
- Patient portals
- Billing software
- Fax machines (yes, these still count)
- Mobile devices, tablets, and laptops
- USB drives and external storage
- Paper-to-digital scanning workflows
- Backup systems and disaster recovery storage
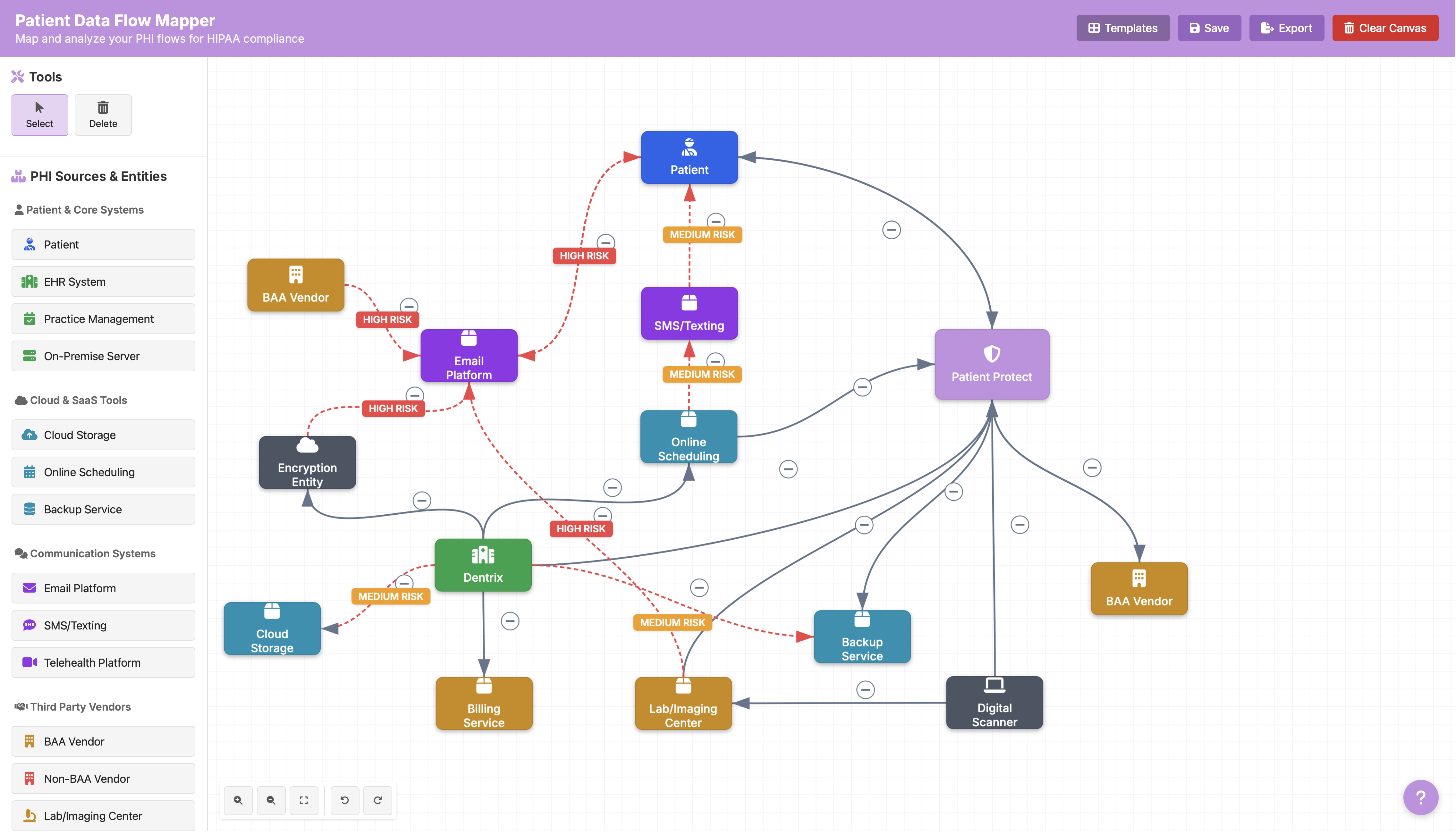
The ePHI data flow mapper is a free tool that walks you through this inventory step by step. If you have not mapped your ePHI flows, start there.
Identify threats to each system
For every system on your list, document what could go wrong. HIPAA requires you to consider threats across three dimensions:
- Confidentiality — unauthorized access to PHI (hacking, snooping, lost devices)
- Integrity — unauthorized alteration of PHI (ransomware, accidental deletion, software bugs)
- Availability — loss of access to PHI when needed (ransomware, system failure, natural disaster)
For independent practices, the threat landscape typically includes phishing attacks, ransomware, lost or stolen devices, unauthorized employee access, vendor breaches, and social engineering. Attacks on independent providers have risen 6x since 2021 — you are not too small to be targeted.
Assess likelihood and impact
For each threat, estimate how likely it is to occur and how severe the impact would be. This does not require statistical modeling. It requires honest evaluation. A dental practice with no email encryption and staff who regularly email patient records has a high-likelihood, high-impact risk — and it needs to be documented that way.
Document existing controls
What safeguards are already in place? Encryption, access controls, training, physical locks, antivirus, firewalls. These controls reduce risk but do not eliminate it. Document what is working and what has gaps.
Determine residual risk and mitigation plans
After accounting for existing controls, what risk remains? For each residual risk, document a mitigation plan: what will you do, by when, and who is responsible. This is where the risk assessment becomes a management tool, not just a compliance artifact.
Why annual is not enough
The Security Rule does not specify a frequency for risk assessments — it says "periodic." Most practices interpret this as annual. That is a floor, not a ceiling.
You should reassess risk whenever:
- You adopt a new technology (new EHR, new cloud service, new patient portal)
- You change business associates or vendors
- A breach or security incident occurs — at your practice or at a peer organization
- Staff turnover affects access controls
- You expand locations or services
- Regulatory changes alter the threat landscape (such as the proposed 2025 HIPAA Security Rule amendments)
The Change Healthcare breach — which exposed more than 190 million patient records and caused more than $2.8 billion in losses — prompted thousands of practices to reassess vendor risk. If your practice used Change Healthcare and did not update your risk assessment after that event, you have an active gap.
The HHS SRA Tool is a starting point, not an endpoint
HHS offers a free Security Risk Assessment Tool. It is better than nothing, but it has significant limitations. The tool is designed for very small practices, it does not score or prioritize risks, and it produces a static document rather than a living compliance artifact. We covered this in detail in The HHS SRA Tool Isn't Enough.
The free risk assessment tool on our platform goes further — it maps your specific environment, scores risks by severity, and generates a prioritized remediation plan.
Documentation that holds up to OCR audit
When OCR investigates, they are not looking for perfection. They are looking for evidence that you took reasonable steps to identify and address risk. Your risk assessment documentation should include:
- Date and scope — when the assessment was conducted and what was evaluated
- Methodology — how you identified threats, assessed likelihood and impact, and determined risk levels
- Findings — specific threats, vulnerabilities, and risk ratings for each system
- Current controls — what safeguards are in place
- Remediation plan — what you will do about gaps, with timelines and responsible parties
- Management sign-off — evidence that leadership reviewed and accepted the findings
A practice that conducts a thorough risk assessment and documents honest gaps with remediation timelines is in a dramatically stronger position than a practice that produces a perfect-looking form with no substance behind it.
From risk assessment to risk management
The risk assessment tells you where your exposures are. Risk management is what you do about them. Steps 3 through 17 of this series address the controls — policies, training, access controls, encryption, incident response — that reduce the risks you identify here.
But those controls are only as good as the assessment that informs them. If you skip this step or treat it as a paperwork exercise, every downstream control is built on guesswork.
Healthcare breaches cost an average of $9.8 million. For independent practices, the consequences often look different — not a nine-figure settlement, but a practice that closes. Thirty-five to forty percent of small practices that suffer a breach close within two years. The risk assessment is your first line of defense against becoming that statistic.
Resources
| Resource | Description | |---|---| | HHS Risk Assessment Guidance | Explains the scope and requirements for risk analysis under the HIPAA Security Rule | | OCR SRA Tool | A downloadable tool from the Office for Civil Rights to help small practices conduct a HIPAA Security Risk Assessment | | NIST SP 800-30 | Risk assessment framework often used by larger health systems and compliance professionals |
This is Step 2 of our 17-step HIPAA compliance roadmap. Previous: Step 1 — Know Your HIPAA Status. Next: Step 3 — Build Bulletproof HIPAA Policies.
