17-Step HIPAA Compliance Series
Lock Down Physical Access to ePHI (Step 4 of 17)
Step 4: Secure physical access to ePHI — manage devices, enforce encryption, and reduce HIPAA risk with documented controls.

Physical security is a HIPAA requirement, not a nice-to-have
When practices think about HIPAA security, they think about firewalls, encryption, and passwords. Physical safeguards get treated as an afterthought — a lock on the server closet and a feeling that the office is "secure enough."
The Security Rule disagrees. Physical safeguards are one of the three required safeguard categories (alongside administrative and technical), and OCR has issued enforcement actions specifically for physical security failures. A laptop stolen from an unlocked car. Patient records visible to unauthorized visitors. A server room accessible to cleaning staff.
This is Step 4 of our 17-step HIPAA compliance roadmap. Your risk assessment identified where ePHI lives. Your policies define the rules. Now you enforce them in the physical world.
Facility access controls
The Security Rule at 45 CFR 164.310(a)(1) requires policies and procedures to limit physical access to your electronic information systems and the facilities in which they are housed.
For most independent practices, this means:
Control who enters restricted areas
Not every area of your practice needs the same level of access control. But areas where ePHI is accessible — server rooms, workstations with EHR access, record storage areas — require documented access controls.
- Server/network closets should be locked. Not propped open, not unlocked during business hours, not accessible to anyone who happens to walk by. A physical lock with a key log or keycard access is the minimum standard.
- Workstation areas should be positioned so screens are not visible to patients, visitors, or unauthorized personnel. If your front desk faces the waiting room and the screen shows patient schedules, that is a physical safeguard failure.
- Record storage — both paper and electronic media — should be in controlled areas with documented access.
Visitor management
Every practice has visitors: vendors, IT technicians, sales reps, delivery personnel, inspectors. The question is whether those visitors can see or access PHI during their visit.
- Maintain a visitor log for non-patient visitors in clinical and administrative areas
- Escort visitors in areas where PHI is accessible
- Ensure cleaning and maintenance crews do not have unsupervised access to workstations, servers, or record storage during off-hours
You do not need airport-level security. You need documented procedures and reasonable controls that match your practice environment.
Workstation use and security
The Security Rule requires two related standards: workstation use (164.310(b)) and workstation security (164.310(c)).
Workstation use
Define what functions can be performed on each workstation and how those workstations should be used. Practical requirements:
- Workstations accessing ePHI should not be used for personal browsing, personal email, or unauthorized software
- Screens displaying PHI should not be visible to unauthorized individuals — use privacy screens, position monitors away from public areas, or use automatic screen blanking
- Staff must log off or lock workstations when stepping away — every time, without exception
Workstation security
Protect the physical workstation itself:
- Secure workstations to desks or furniture with cable locks where theft risk exists
- Position workstations in areas with controlled access
- Ensure laptops used for ePHI have full-disk encryption (this crosses into Step 5, but the physical control of the device starts here)
Device and media controls
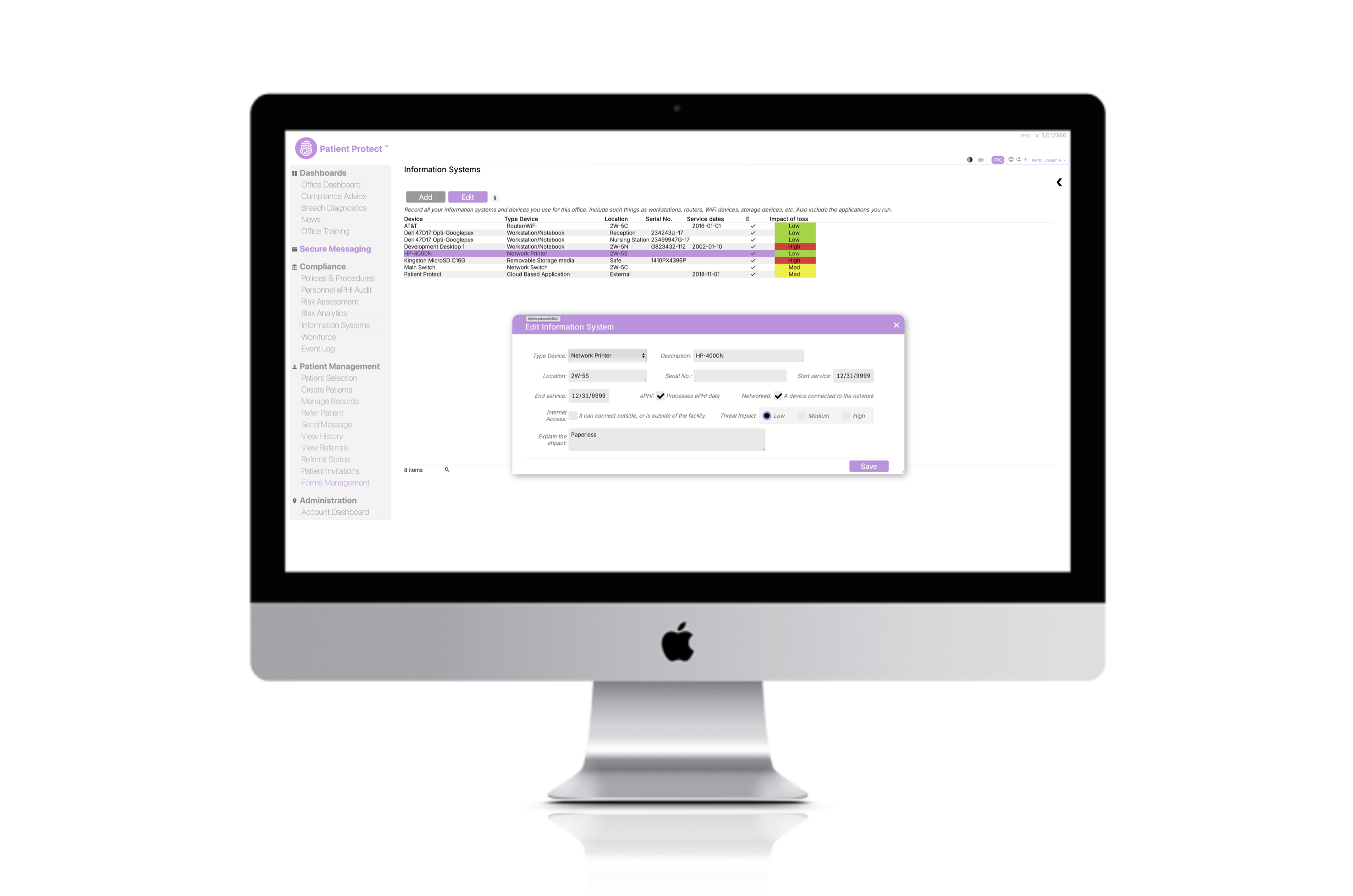
The Security Rule at 164.310(d)(1) requires policies governing the receipt and removal of hardware and electronic media that contain ePHI. This applies to the full lifecycle of every device that touches patient data.
Disposal
When a device reaches end of life — a retired workstation, a replaced hard drive, a decommissioned server — the ePHI on it must be destroyed. Not deleted. Destroyed.
- Hard drives: Degauss, physically destroy, or use DOD-standard wipe procedures
- SSDs: Cryptographic erasure or physical destruction (standard overwrites are unreliable on SSDs)
- Mobile devices: Factory reset is insufficient — use manufacturer-recommended secure erase
- Paper records: Cross-cut shred. Straight-cut shredding is not sufficient for PHI
- Copiers and printers: Modern multifunction devices have internal hard drives that store copies of every document processed. These must be wiped or destroyed at end of life.
Document every disposal. Record the device, the method, the date, and the person responsible.
Re-use
Before reissuing a device to a new user, all previous PHI must be removed. This applies to workstations reassigned between staff, loaner laptops, and shared devices.
Movement
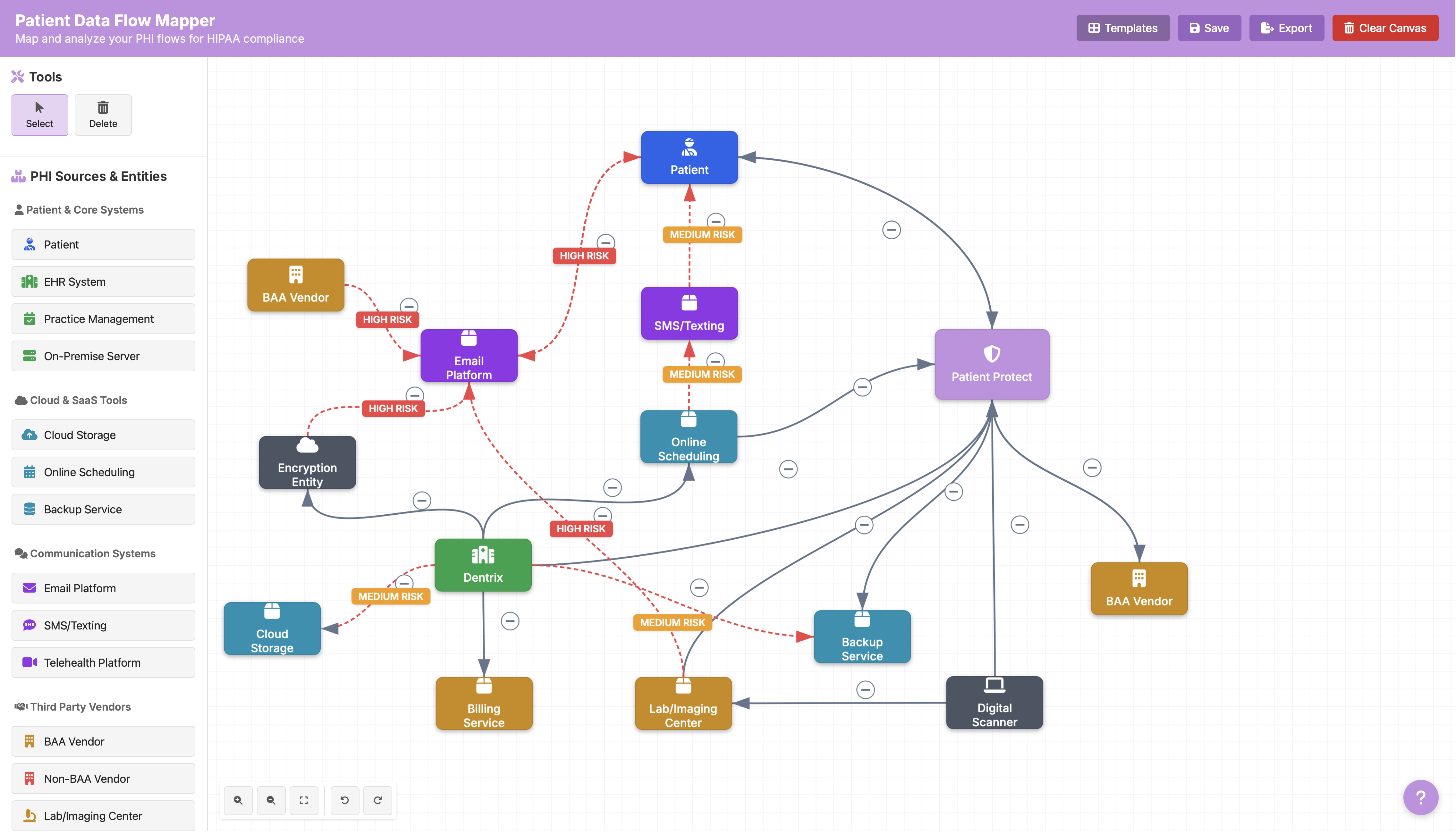
When devices containing ePHI move between locations — a laptop going home with a provider, a backup drive transported to off-site storage — document the movement and ensure appropriate encryption is in place. The ePHI data flow mapper helps you track where devices and data move across your environment.
The physical security audit checklist
Walk through your practice with fresh eyes and evaluate:
- [ ] Server/network equipment is in a locked room or closet
- [ ] Workstation screens are not visible to unauthorized individuals
- [ ] All workstations have automatic lock/timeout configured
- [ ] Privacy screens are installed where needed
- [ ] Paper records with PHI are stored in locked cabinets
- [ ] Fax machines receiving PHI are in controlled areas (not open hallways)
- [ ] Printers used for PHI output are in controlled areas
- [ ] A visitor log exists and is maintained
- [ ] Device disposal procedures are documented and followed
- [ ] Cleaning/maintenance access to PHI areas is supervised or controlled
- [ ] Laptops and portable devices are secured when not in use
- [ ] End-of-life devices are tracked through disposal
If any of these items reveal gaps, document the findings in your risk assessment and create a remediation plan with a timeline. An identified gap with a plan is infinitely better than an unidentified one.
Common physical security failures in independent practices
The EHR on the reception counter. Front desk monitors angled so patients in the waiting area can read appointment details. A privacy screen costs $40. The lack of one can cost you a corrective action plan.
The unlocked server closet. "We keep it unlocked so the IT guy can get in." Give the IT provider a key or a code. Keep it locked.
The retired laptop in a drawer. Old devices that still contain ePHI, sitting in desk drawers or storage closets with no plan for disposal. Every one is an unencrypted breach waiting to happen.
Paper at the printer. Lab results, prescriptions, and referral letters sitting in the output tray of a shared printer in an open area. Move the printer or implement pull-printing.
Physical security is the foundation for digital security
You cannot protect ePHI digitally if the physical environment is compromised. An encrypted server behind an unlocked door. An EHR with perfect access controls on a workstation visible to the waiting room. Full-disk encryption on a laptop that walks out the door because no one noticed it was missing.
Physical safeguards are where compliance meets the real world. Get them right, and every technical control you implement in the steps ahead operates on a secure foundation.
This is Step 4 of our 17-step HIPAA compliance roadmap. Previous: Step 3 — Build Bulletproof HIPAA Policies. Next: Step 5 — Secure Devices and Endpoints.
